Recent Posts
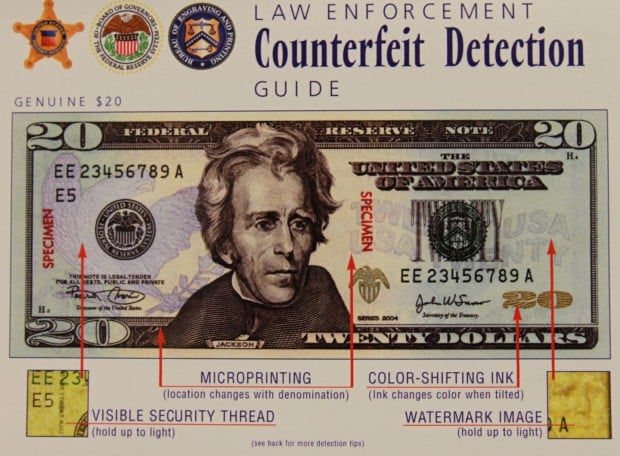
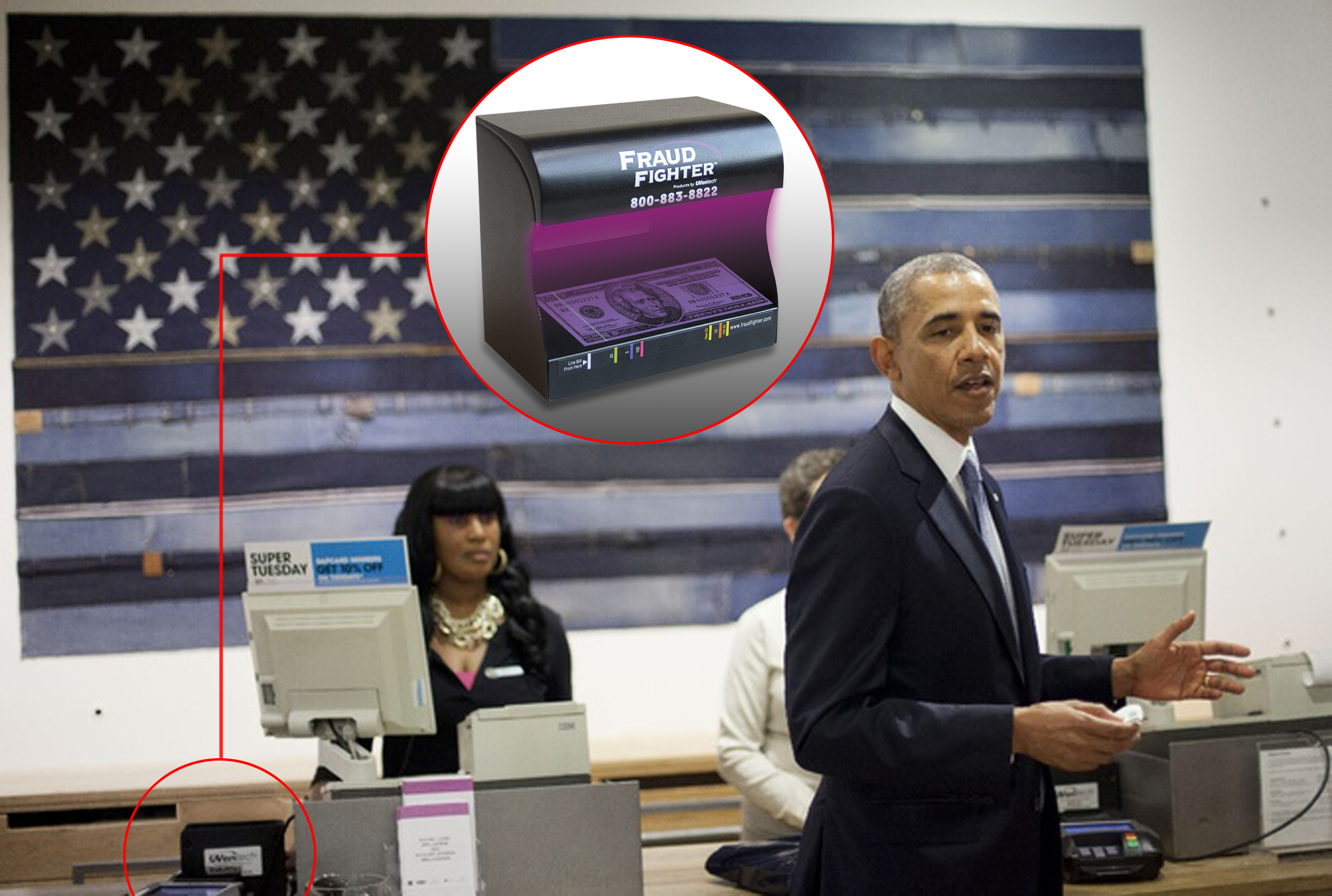
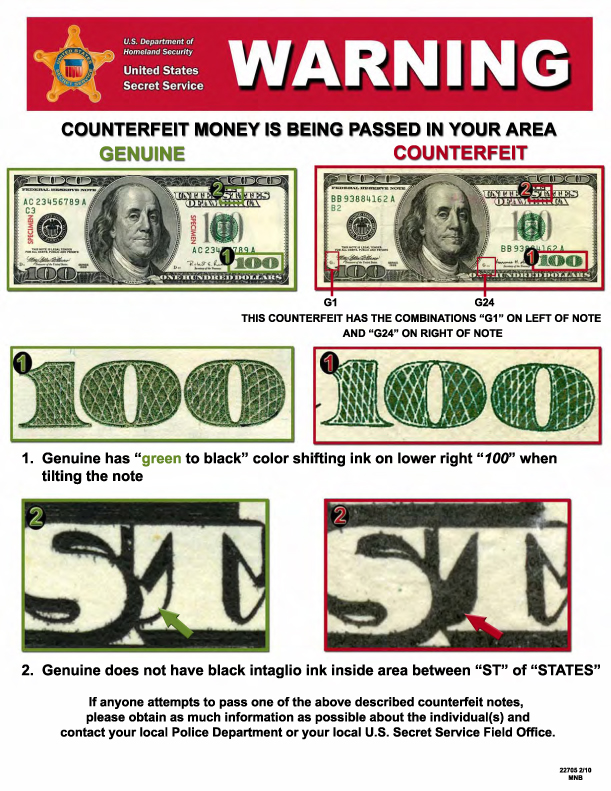
How to Spot Counterfeit Cash and Protect Your Business If you run a business—or even just handle...
Earlier this year, I was presenting at the IAFCI (International Association of Financial Crimes...
As the name suggests, the purpose of the Federal Trade Commission’s Standards for Safeguarding...
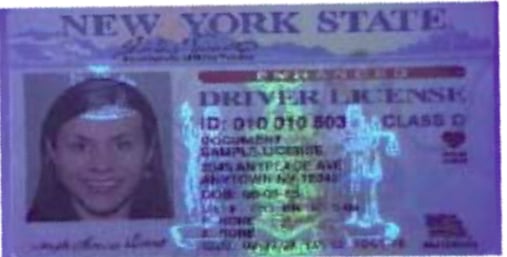
Recent trends in fraud have created the imperative to authenticate the identity of your customers...
In the fast-paced world of real estate, it's essential to stay one step ahead of fraudsters.Real...
Glendora, CA – Tuesday, September 19, 2023 – UVeritech, Inc announced today that it has achieved...
Glendora, CA – Friday, July 22, 2022 – UVeritech, Inc announced today that it has achieved SOC 2...
Here’s a real-life scenario that one of our customers described to us - The shipping yards operated...
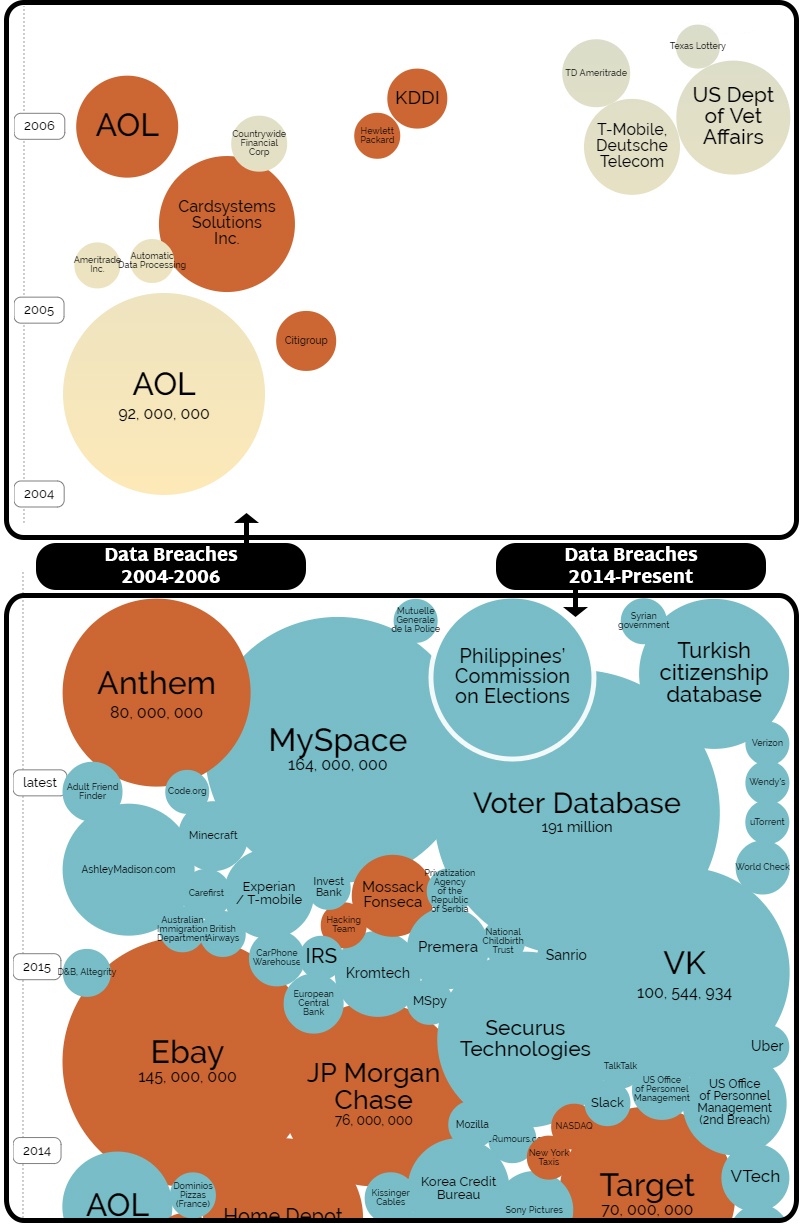
The rate at which Identity Theft is growing in the United States is nothing less than shocking....
Incidences of Identity-Theft Related Cargo Theft are on the rise
There is a surprising range of counterfeit detector options available in the marketplace today....
What is ATO Fraud? Account Takeover (ATO) fraud begins as theft of consumer account...
LexisNexis (LN) recently released its Financial Services & Lending focused 2022 True Cost of Fraud...
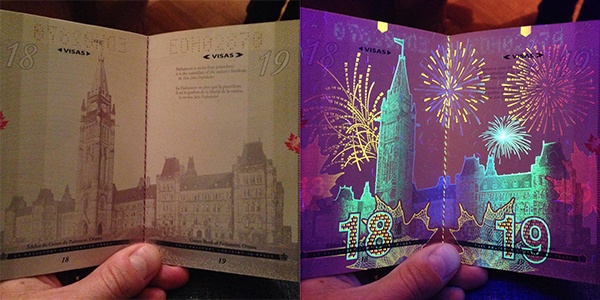
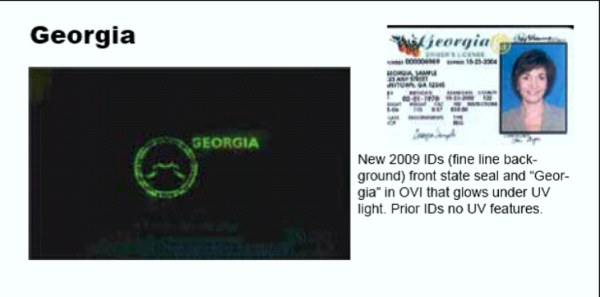
Countries around the world are designing ever-more intricate (and beautiful!) UV security features...
Employees tasked with running cash registers and point of sale (POS) systems are a store’s first...
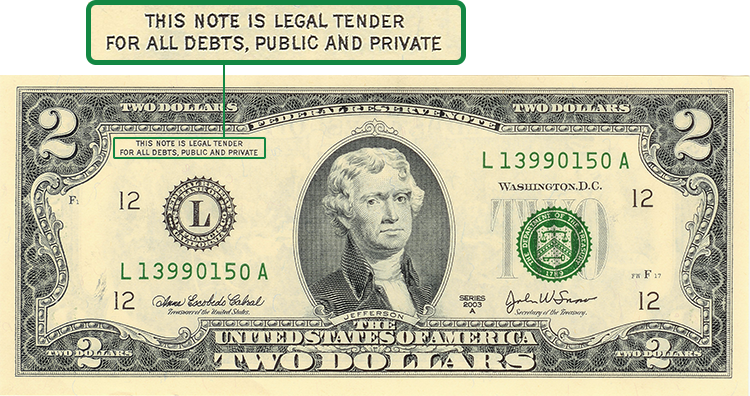
A quick perusal of recent news stories using the keyword “counterfeit money” reveals the most...
Two Packages, $136K of Counterfeit Currency CBP Officers in Chicago Seize Shipments Containing...
It is often said that the act of counterfeiting money is as old as money itself. No matter the type...
Fraudulent transactions have grown step-for-step with legitimate economic activity – and is booming...
Cashiers and Tellers Report Unable to “Feel” whether Money is Real or Not During our twenty years...
When it comes to assessing your risk of identity theft and fraud, being digitally compromised in a...
Several weeks ago, we began getting calls from a few clients asking us whether specific versions of...
Terrifying financial horror stories aren't fiction!
I found the below article so compelling, and so important as it relates to the current environment...
How the release of personally identifying information (PII) of nearly half the US population should...
Retailers are on course to lose more than $70 billion globally to remote “card-not present” (CNP)...
• TABLE OF CONTENTS •Common ATO Attack TargetsMillennials Seriously Question what Large...
• TABLE OF CONTENTS •CNP FraudIdentity Fraud via Phishing, Malware, and Social MediaOther Identity...
• TABLE OF CONTENTS •Remote BankingMobile Client Onboarding is the Next FrontierMobile Identity...
• TABLE OF CONTENTS •What does the future of financial services look like?Millennials Seriously...
Identity Theft continues to rank as the fastest growing form of fraudulent crime A recent report by...
Mobile Identity Authentication Many potential business-cases point to the desire to have an...
Identity fraud is rampant. Just perform a Google search on the term and the evidence to support...
Earlier this year, a car salesman in Houston was kidnapped while taking a prospective client on a...
It was last year that I heard a prominent loss prevention professional - a name that many in the...
For many years, credit card fraud has been the favored method for fraudsters seeking to profit from...
Most people have some exposure to fraud deterrents in their daily lives. For the honest person,...
Young people who are under the drinking age have long looked to fake IDs to get around the law....
To combat the recent tidalwave of identity theft cases across the United States, the Internal...
With the increase of mobile commerce brings a parallel increase in fraudulent mobile transactions,...
Fraud is big business.The Federal Trade Commission has estimated that 10.8 percent of U.S. adults...
According to a new report, the majority of online fraud in the United States is coming from several...
When it comes to summer safety tips, identity theft and fraud may not be the first things that come...
In a short new series, Fraud Fighter will profile a variety of high-fraud cities across the country...
In our tech-based society, smartphones, tablets, and other mobile devices are central to our daily...
No matter how careful you've been to protect your personal data and information, there are still a...
Modern counterfeit detection relies on a wide range of specialized detectors, but there is a...
FraudFighter Products offers solutions to organizations that are concerned with verification of...
We often assume that major identity theft issues come from data breaches or scammers - but have you...
Scientists out of the National University of Singapore have found a method of utilizing nanohole...
We'd all like to assume that we are quick enough to recognize a scam before falling into a trap -...
Financial institutions have long been the target of phishing schemes and fraudulent activity- from...
Identity theft and fraud among senior citizens is rising across the country, with many states as...
With recent data breaches across massive retailers from Target to Home Depot, you might be...
The United Kingdom is reporting a huge jump in liability fraud, citing a 75% increase in bogus...
As the Internal Revenue Service continues to work to combat tax fraud this year, other federal...
Counterfeit money has been around as long as authentic money. Even some of the very first western...
Many individuals who are on the market for a new job are fearful of the risks that come along with...
When it comes to identity theft, your children are likely not the first ones you might worry about....
The Better Business Bureau of Connecticut is warning job seekers to watch out for examples of...
Despite the Securities and Exchange Commission's focus upon regulating the securities industry and...
In a wave of preventative measures for data protection, the Blue Cross Blue Shield Assocation...
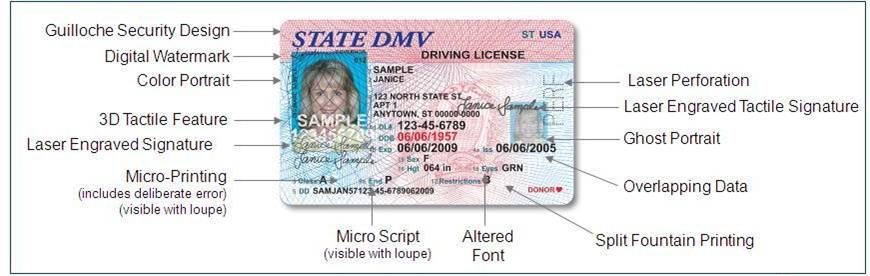
Accurate identification papers are essential to safeguarding financial and legal transactions as...
Identity theft issues continue to plague the Internal Revenue Service, and the U.S. Treasury...
Counterfeiting and identity theft are major concerns for the public, and safety of private...
Millennials probably don't worry too much about identity theft or fraud -- but according to a...
Following a recent online attack that resulted in the diversion of tax refunds and the theft of...
For as long as governing bodies have released official documents and notes, counterfeiting has been...
Forged Document Detection as a Central Loss Prevention Strategy As highlighted in last week's...
Deep in the underbelly of the "Dark Web's" digital black market, identity fraud and counterfeiting...
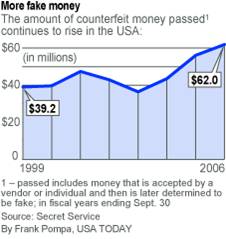
Counterfeit money damages the U.S. economy and can substantially impact businesses of all...
When an identity is stolen, the damage can extend far beyond the credit report of the victim. When...
The modern era of counterfeit money production has enabled anyone with a home computer, a scanner...
In 2013, the U.S. government says it recovered more than $88 million in counterfeit currency in the...
Loss prevention is a many-faceted practice these days. Gone are the times when cameras on the...
Does your business handle in-store credit applications? Are you verifying the identifications of...
Astonishing expose published in GQ Magazine I read a very fascinating article published in GQ this...
I was having lunch with my friend, Crystal, the other day and she says to me “Oh, hey. You’ll find...
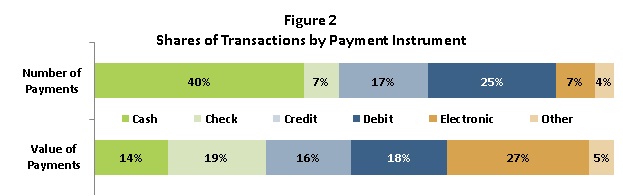
It is a widely held belief these days that the end of the “cash economy” is upon us. With rapid...
$13,000 Rental by 19 year old triggers disbelief, outrage Many people were shocked and amazed...
We have reported much in recent months regarding the increasing sophistication of ID thieves, and...
Earlier this year, the European Central Bank (ECB) revealed that a record 670,000 counterfeit notes...
I get news-clippings everyday from Google. It's quite amazing, actually, this ability to have a...
Would You Have checked his $100 Bill for Counterfeit? When training your workers to detect and...
Warning:The following information is scary. Stop reading now unless you have a robust identity...
We have written much on the subject of the Modern Face of Identity Theft, and howtechnological...
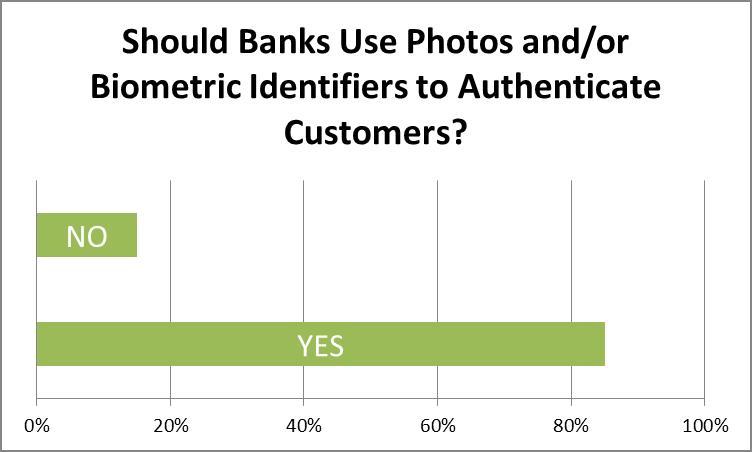
Identity authentication is rapidly becoming an issue of great concern to the banking and other...
Trading Electrons The latest term trending in the financial world is cryptocurrency. Loosely...
Sharp Spike in Fraudulent Tax Returns Reported by IRS
Reports Already Coming-In about the New $100 note "falling apart'
Our nuclear plants have become like mini-fortresses following 9/11. Concerns over attacks on land...
The United States has launched a new $100 bill as of October 8, 2013, the first remake of the...
FBI Seizes and Shuts-Down "Silk Road" a leading dark market website. A Federal complaint revealed...
This article was originally published on CBinsight.com The Best Way to really "Know Your...
New Report by Tufts University Details Costs of Cash-Economy to both Businesses and Individuals I...
Yet Another Production Delay may Affect Release Date for New $100 Bill New Anti-Counterfeiting...
Fluorescent Security Feature On New $100 to be Identical to Previous $100 Bill, Only Better.
According to FBI statistics Identity Theft is the nation's fastest growing crime. Identity theft...
Every day, I get news clippings - courtesy of Google news - on the topic of counterfeit money. The...
In early June this year, we conducted a survey of banking and financial professionals, asking...
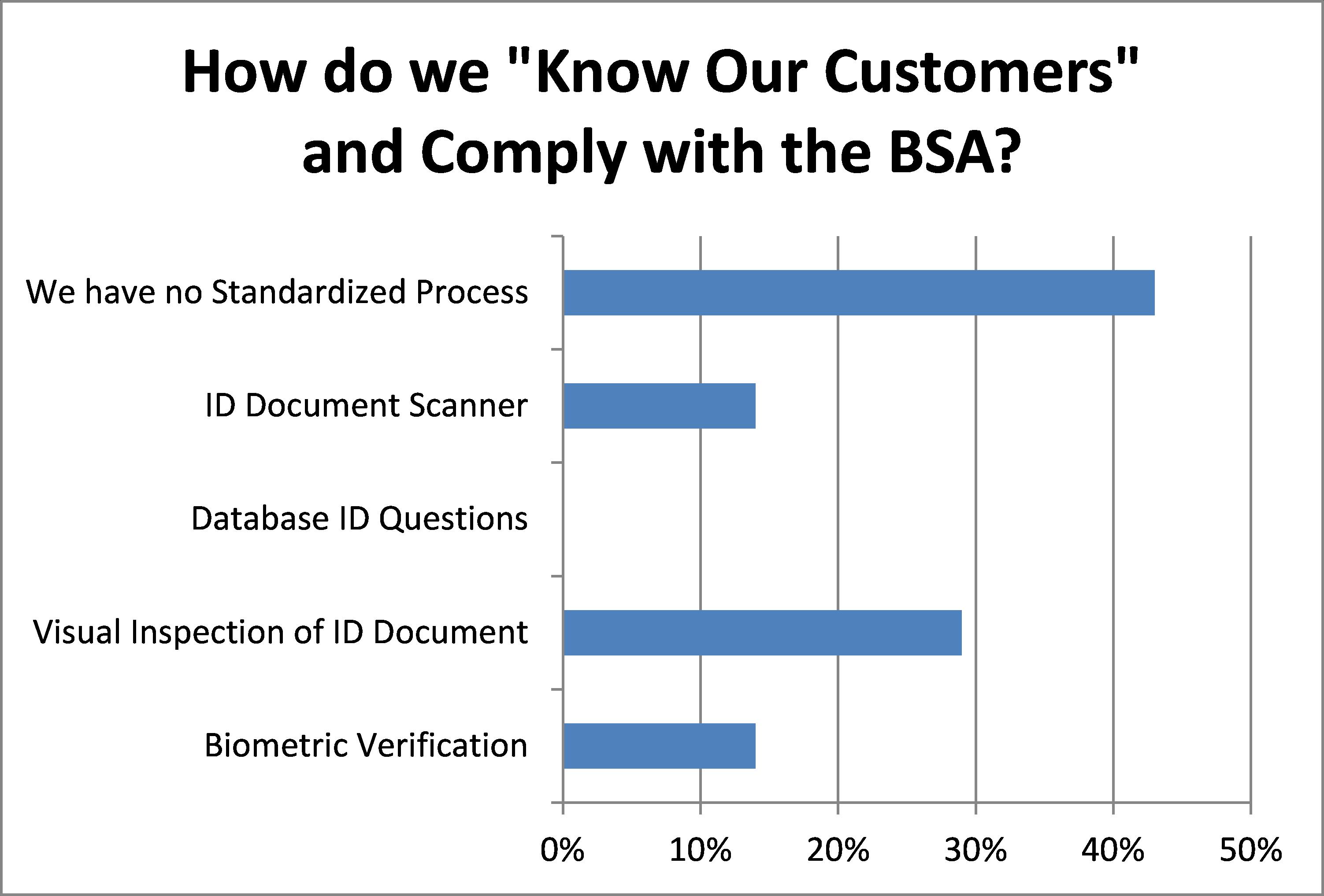
In a survey of financial professionals conducted last month, FraudFighter discovered that a vast...
The U.S. Treasury Department's Bureau of Engraving and Printing (BEP) announced that the...
Over the past 14 months, the Bank of Canada has released a series of newly designed banknotes. The...
Faced with the extraordinary challenge of trying to bring a financial services operation into...
Financial Services Industry needs to become Global Leaders in Identity Authentication Over the...
When you sign up for something online, whether it's a social media site, shopping platform or...
People send me articles, news stories and reports all the time. Part of the fun (and, burden) of...
I really can't give the Federal Reserve or the Bureau of Engraving and Printing a hard time. The...
I read an interesting Article yesterday on Motley Fool, one of the sites where I go for relevant...
Bank Secrecy Act compliance is more important than ever to companies that deal with “covered...
Fraud and data security breaches come in so many different forms and from so many different...
Simply put, multi-layered fraud prevention means that you must seek to understand the...
The results are in, and even we have to admit that we are astounded by what has happened.
According to a recent survey of major U.S. retailers, conducted by the National Retail Federation,
The Federal Trade Commission reports that over 9 million Americans are victims of identity theft...
Halloween is over and the holiday season is upon us. This means retailers should expect large...
Peru Supplies 1/3 of all Counterfeits in U.S. Last month Peruvian authorities, in conjunction with...
Knowing how to spot fake money is a skill that every cash handler should know. With advances in...
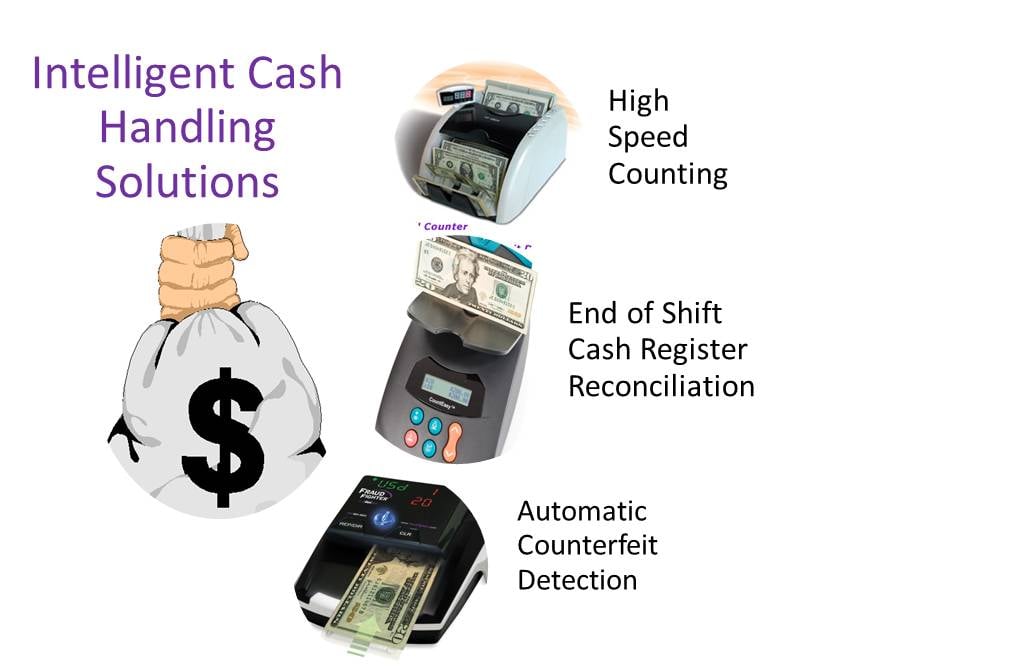
Money counting is a matter of time and accuracy. Either you save time with the CountEasy(tm) Scale...
There are a number of ways to achieve compliance with anti money laundering regulations by...
Many of our customers ask us - Why is the UV security feature on the $100 bill more difficult to...
As technology advances and as more people become aware of the simplicity of digital
If Internet conversation is any indication, businesses and consumers continue to harbor fears of...
Anyone that has been in retail for any length of time knows that protecting your company's assets...
To deter or prevent illegal activity including terrorism and money laundering, Bank Secrecy Act...
The Bank Secrecy Act or BSA requires a written Customer Identification Program (CIP) for client...
Companies lose billions of dollars every year to counterfeiters who are clever enough to print...
(BSA) Bank Secrecy Act and (FACTA) Fair and Accurate Credit Transactions Act: Red Flag Rules ...
Here are three easy steps you can take, right now, with no cost and very little time investment...
"Get Money" isn't just a song by The Notorious B.I.G.
Passing Counterfeit Money Through Retailers is a Multimillion Dollar Industry Every year,...
Manually counting cash is one of the best ways to lose money in your retail business. Cash...
No Update From the Treasury Since June 2011 The U.S. Treasury has yet to announce a release date...
In 2009 the U.S. Treasury reported that over $400 Million in counterfeit currency was...
For as long as people have used paper currency, there have been attempts to counterfeit it. In...
The best way to detect a counterfeit bill often depends on the context, such as the type of...
At the heart of many acts of fraud lies the intentional misrepresentation of identity. When ORC...
Every year, retailers lose between $15-30 billion from Organized Retail Crime (ORC). It may sound...
Most loss prevention and asset management personnel make the mistake of thinking that shrinkage...
Most people associate the United States Secret Service with the protection of the President and...
Counterfeit currency. Not something most of us think about. We think we know what it is and some...
Loss. Whether it happens in the form of shoplifting, cash register shortages, product shrinkage...
In today's economy, organization - from "mom and pop" stores to giant retailers - are looking for...
In a recent speech to the GOP faithful, Presidential Candidate Mitt Romney held up Arizona’s...
Desktop publishing to make money: A simple business concept used either to supplement income or...
Judging by the number of Google searches devoted to it, counterfeit money continues to be a big...
Counterfeit money. According to the United States Secret Service, $261 million in counterfeit...
The world has changed much since September 11, 2001. Awareness of how fragile our way of life can...
In the past, fake ID’s have largely been associated with underage drinkers trying to get their...
Scenario:A financial institution is opening a new branch, and is starting a major local PR blitz...
Criminals interpreted the American prospect of “making money” quite literally in the past month,...
As if it weren’t already difficult enough to verify identity documents, now comes a new wrinkle in...
Earlier this month, FraudFighter began providing advanced sample copies of our new Driver License...
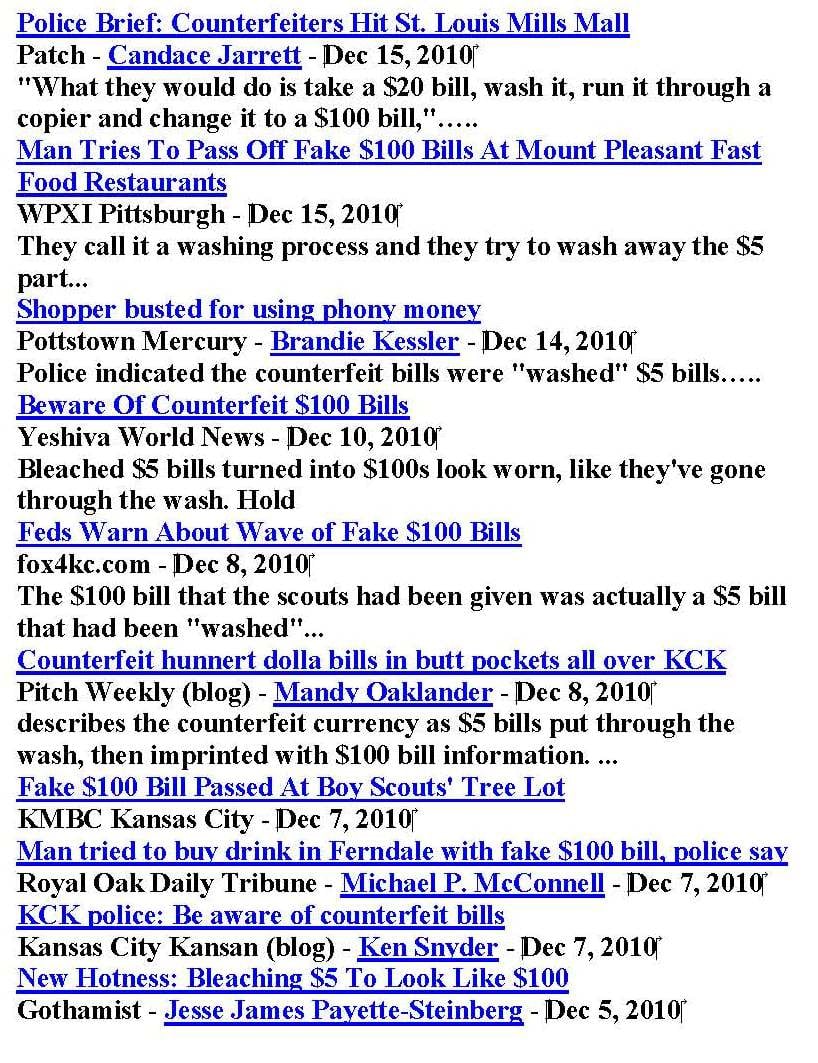
A few days ago, I typed the words “Washed $100 Bill” into Google News, and below is the first page...
In an interesting Nov 25th article in Time Magazine, author Lucien Chauvin describes how Peru has...
Fraud Fighter's Latest Innovation Passes the Test
Mortgage fraud has been much in the news in recent years. After the dust created by the...
Earlier this week we discussed how financial institutions place improper focus on online identity ...
There’s a lot of semantic debate these days over what to name foreign nationals who violate U.S....
In a startling revelation yesterday, one of the largest U.S. banks admitted in court that a...
In another great article on the National Retail Federation blogsite, Ellen Davis discusses return...
Burden, or Benefit?
Part 4 of a four-part Process for Setting-up a Red Flag Rules Compliance Policy UPDATING THE...
Casino environments are beset by opportunities to experience losses from counterfeit fraud....
If your organization is involved in the financial services industry, or in any way has a regular...
This is the first in a series of articles discussing the challenges faced by casinos - regarding...
Part II of a Four-Part Procedure for Compliance with Identity Theft Prevention Requirements If your...
Part I of a Four-Part Procedure for Compliance with Identity Theft Prevention Requirements
NRF Loss Prevention Blog Article In a very interesting blog article found an the National Retail...






.png)

.png)