identity theft
In the middle of a busy Tuesday afternoon, the shipping manager at a regional logistics hub...
If you thought losing your phone was bad, imagine losing your entire identity. That’s what happened...
Earlier this year, I was presenting at the IAFCI (International Association of Financial Crimes...
No one wants to face a significant loss, especially in the equipment rental industry where the...
You might be asking yourself; do I really need to pay for another service? Sometimes it seems like...
The reality is identity fraud has and will continue to rise. Over recent years, we have seen...
Car theft has been a persistent issue for decades, causing significant financial losses and...
Nearing the end of Q2 in 2023, it seems like fraud is already abundant. T-Mobile had yet another ...
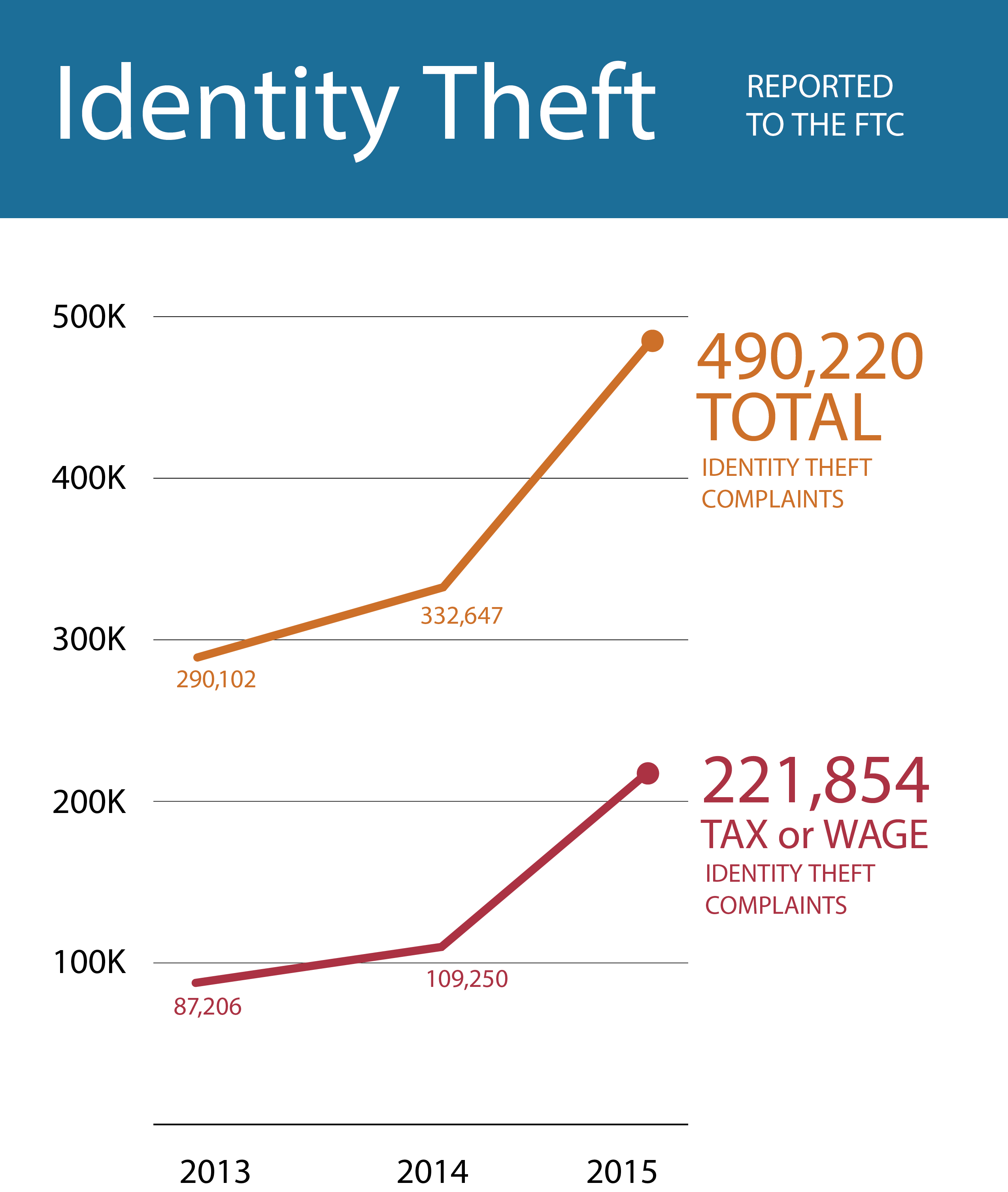
Identity theft cases are on the rise. Again. Year after year cases continue to skyrocket and are...
What is a Notary Public?
Underage drinking. We all know it’s a problem, but how prevalent is it really? According to the USA
A customer walks up to your front desk. They flash an ID and hand over a credit card displaying the...
To stay competitive in the Auto Rental Industry it is essential that the renting process is fast,...
A new March 29, 2022 report by Javelin Research revealed that identity fraudsters continue to steal...
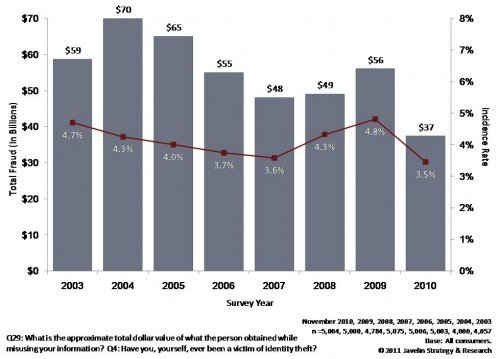
The rate at which Identity Theft is growing in the United States is nothing less than shocking....
As our world continues to shift further into the realm of the internet, so do our buying habits. A...
When the term “Identity Theft” is brought up in conversation, our thoughts usually jump to the pain...
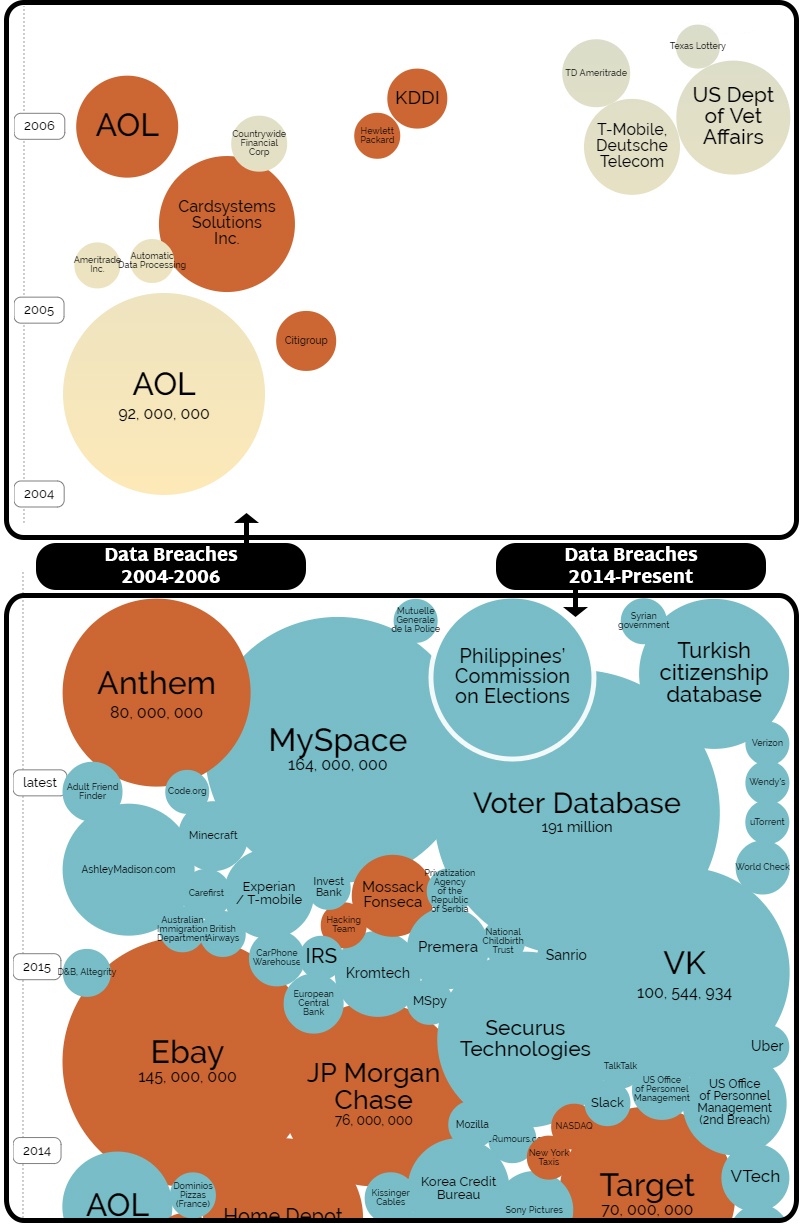
When it comes to assessing your risk of identity theft and fraud, being digitally compromised in a...
Terrifying financial horror stories aren't fiction!
How the release of personally identifying information (PII) of nearly half the US population should...
• TABLE OF CONTENTS •Common ATO Attack TargetsMillennials Seriously Question what Large...
• TABLE OF CONTENTS •What is New Account Fraud?New Account Fraud StatsThe Link between Identity...
• TABLE OF CONTENTS •CNP FraudIdentity Fraud via Phishing, Malware, and Social MediaOther Identity...
Identity Theft continues to rank as the fastest growing form of fraudulent crime A recent report by...
If preliminary estimates hold steady, the amount of fraud victims and the total amount lost to...
If you’ve been paying attention to the news, you’ve probably noticed something: the rapid rise of...
In short, yes, you should be worried – but not too much.
Before the advent of the internet, global electronic communications, and online databases, it was a...
Like most millennials, if you left college tens of thousands of dollars in debt with looming...
Young people who are under the drinking age have long looked to fake IDs to get around the law....
To combat the recent tidalwave of identity theft cases across the United States, the Internal...
Fraud is big business.The Federal Trade Commission has estimated that 10.8 percent of U.S. adults...
In our tech-based society, smartphones, tablets, and other mobile devices are central to our daily...
No matter how careful you've been to protect your personal data and information, there are still a...
We often assume that major identity theft issues come from data breaches or scammers - but have you...
We'd all like to assume that we are quick enough to recognize a scam before falling into a trap -...
Identity theft and fraud among senior citizens is rising across the country, with many states as...
With recent data breaches across massive retailers from Target to Home Depot, you might be...
Many individuals who are on the market for a new job are fearful of the risks that come along with...
When it comes to identity theft, your children are likely not the first ones you might worry about....
The Better Business Bureau of Connecticut is warning job seekers to watch out for examples of...
In a wave of preventative measures for data protection, the Blue Cross Blue Shield Assocation...
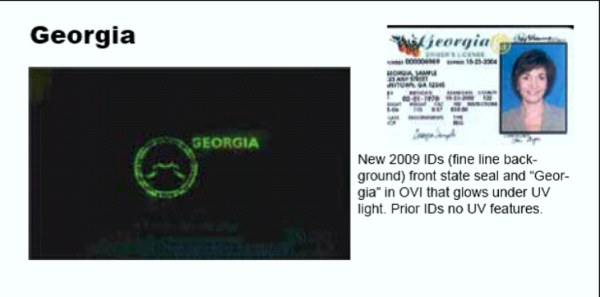
Accurate identification papers are essential to safeguarding financial and legal transactions as...
Identity theft issues continue to plague the Internal Revenue Service, and the U.S. Treasury...
Counterfeiting and identity theft are major concerns for the public, and safety of private...
Following a recent online attack that resulted in the diversion of tax refunds and the theft of...
Recently, in Brooklyn, a man successfully made a $1,500 purchase using fake identification at a...
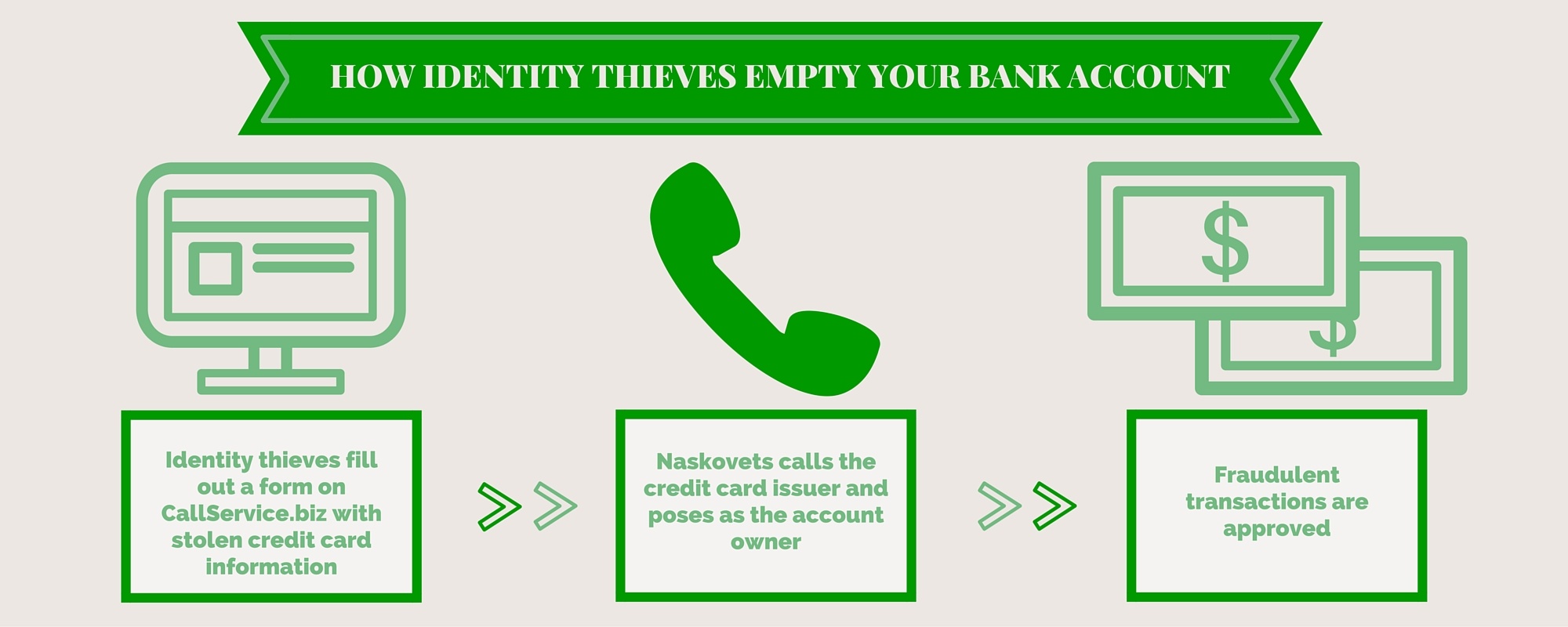
Deep in the underbelly of the "Dark Web's" digital black market, identity fraud and counterfeiting...
At some point, every business should ask itself, “What is the easiest way to prevent fraud from...
Does your business handle in-store credit applications? Are you verifying the identifications of...
The holiday season is nearing meaning the busiest time of the year for retail businesses is...
Tax refund fraud is another form of identity theft that has recently afflicted the IRS. Recently
Warning:The following information is scary. Stop reading now unless you have a robust identity...
We have written much on the subject of the Modern Face of Identity Theft, and howtechnological...
Identity authentication is rapidly becoming an issue of great concern to the banking and other...
Sharp Spike in Fraudulent Tax Returns Reported by IRS
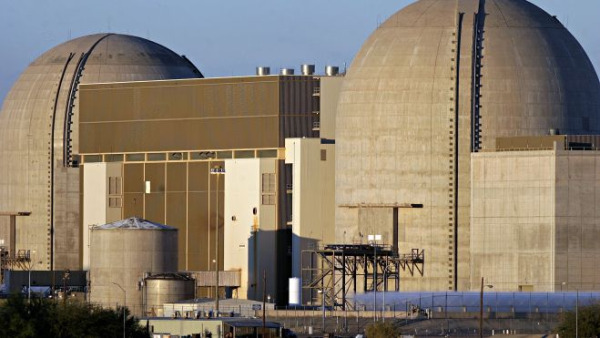
Our nuclear plants have become like mini-fortresses following 9/11. Concerns over attacks on land...
FBI Seizes and Shuts-Down "Silk Road" a leading dark market website. A Federal complaint revealed...
According to FBI statistics Identity Theft is the nation's fastest growing crime. Identity theft...
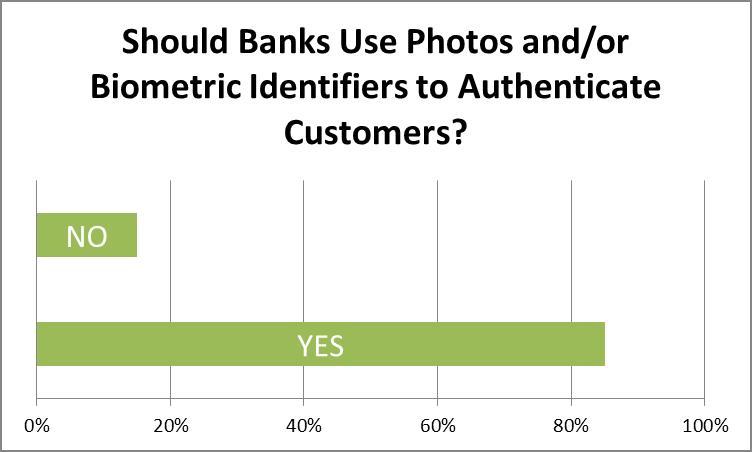
In early June this year, we conducted a survey of banking and financial professionals, asking...
In a survey of financial professionals conducted last month, FraudFighter discovered that a vast...
When you sign up for something online, whether it's a social media site, shopping platform or...
People send me articles, news stories and reports all the time. Part of the fun (and, burden) of...
The Federal Trade Commission reports that over 9 million Americans are victims of identity theft...
In a recent speech to the GOP faithful, Presidential Candidate Mitt Romney held up Arizona’s...
In the past, fake ID’s have largely been associated with underage drinkers trying to get their...
Scenario:A financial institution is opening a new branch, and is starting a major local PR blitz...
Every so often an identity fraud story comes along in the news that is not only impressive in its...
As if it weren’t already difficult enough to verify identity documents, now comes a new wrinkle in...
Earlier this month, FraudFighter began providing advanced sample copies of our new Driver License...
If you read Part I of our blog series on identity fraud you almost surely remember the sum totals...
Two very important studies delving into fraud reports from 2010 were issued recently. The first, a...
Credit card processing servers. Poorly secured corporate networks. Point-of-sale terminals in gas...
Imagine you were offered this amazing business opportunity: you would join an effort by a local...
Good news from the front in the battle against identity theft! Well, somewhat good news. With an...
It is always a treat to hear from actual identity thieves: understandably they are not often...
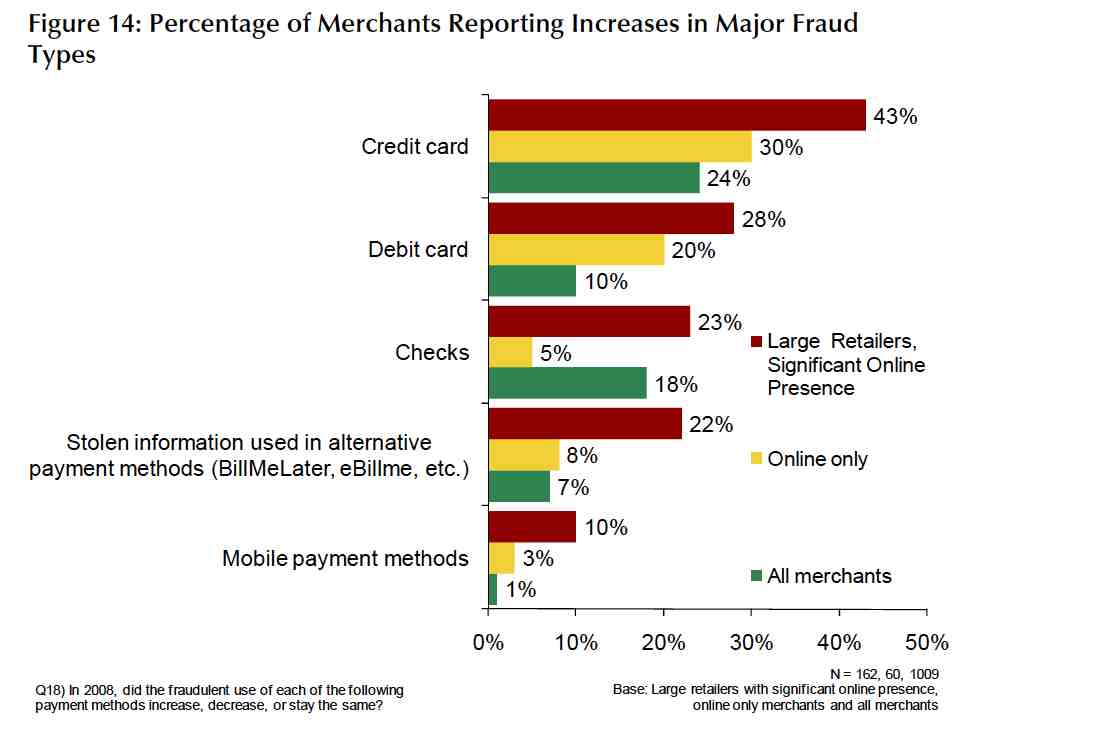
Out of the three groups affected by retail fraud – consumers, financial institutions and merchants...
As we mentioned in our previous post, the impact of retail fraud on businesses and financial...
In continuing our September Mortgage Fraud spotlight, this week we are talking about the...
International Law Enforcement Takes-Down a “Top 10” Site
Big-box stores are a favorite target of fraudsters, because of the value of their products. So...
In another great article on the National Retail Federation blogsite, Ellen Davis discusses return...
Part 4 of a four-part Process for Setting-up a Red Flag Rules Compliance Policy UPDATING THE...
Casino environments are beset by opportunities to experience losses from counterfeit fraud....
If your organization is involved in the financial services industry, or in any way has a regular...
This is the first in a series of articles discussing the challenges faced by casinos - regarding...
Part II of a Four-Part Procedure for Compliance with Identity Theft Prevention Requirements If your...
Part I of a Four-Part Procedure for Compliance with Identity Theft Prevention Requirements
NRF Loss Prevention Blog Article In a very interesting blog article found an the National Retail...