Earlier this week we discussed how financial institutions place improper focus on online identity verification. Too many FI’s suffer from an over-reliance on electronic databases used to match data points – such as addresses and social security numbers – provided by the customer against what is stored in the verification database. This system can be, and as we have showed in our previous posting, already have been defeated.

Anybody can learn enough of their potential identity theft victim’s data to pass a database test. Even unskilled identity thieves can easily find and replicate the information that is used to "verify" the identity of an individual through such electronic database checks. A search engine hunt for a person's full name can result in multiple web links to services that will, for approximately $25, report the address history and relatives list of the person.
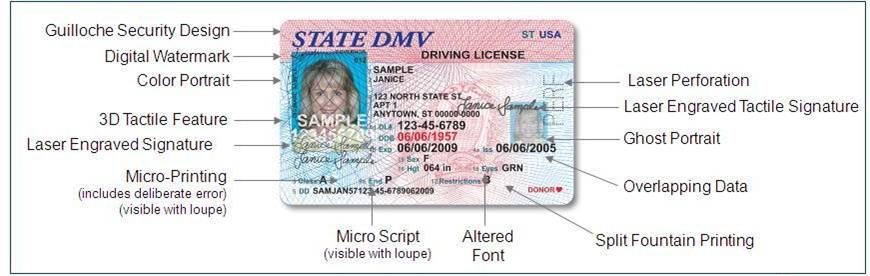
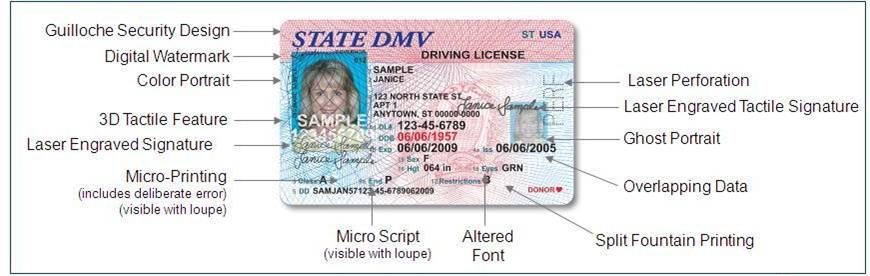
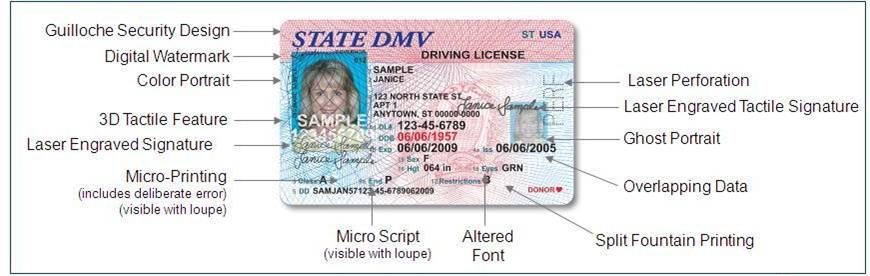
Actual authentication of an identity document can be a more cost-efficient and more effective solution. Rather than looking at customer information, advanced ID authentication technologies will instantly authenticate the identity document itself. A quick digital snapshot of a passport or driver license will compare the imaged results against a list of expected physical attributes – holograms, ultraviolet text, digital security features, invisible text or 3D objects – and reveal whether or not the document is real with accuracy as high as 98%. Documents failing this test can automatically red-flag transactions and prompt the bank or financial institution to ask the customer for additional supporting documentation.
Stealing information is easy for criminals; placing it onto a convincing-looking document is more difficult, but not uncommon. Creating a counterfeit identity document capable of passing advanced optical examination is near impossible. Currently, in the U.S. alone, there are nearly 1,050 different types of “valid” identity document, counting driver licenses, state ID cards, military cards, law enforcement ID’s, diplomatic identity, passports and others.
The upshot to this process for banks, mortgage companies and other financial institutions is obvious – authentication is more precise, and less costly when fraudulent transactions can be stopped at the earliest stages rather than after the transaction has already occurred. There are also additional not-so-obvious advantages:
- Unlike traditional database services, Fraud Fighter's technologies do not work on a “fee-per-transaction” basis. Every model sold is owned and operated exclusively by the institution, providing considerable savings over time – for a method that is significantly better in every way at detecting fraud.
- Identity verification can cross over into other areas of operation: whether for new account openings, wire transfer or other covered transaction types requiring customer identity verification under BSA, FACTA and CIP rules. Using the equipment for these purposes increases returns on investment because – again – no per-transaction fee is incurred.
Because of the constantly changing domain of identity documentation, any genuine identity authentication solution must offer an extensive, inclusive document library that is updated on a regular and frequent basis. By meeting these needs, complete document authentication solutions allow financial institutions to quickly, efficiently, and reliably authenticate the thousands of different identity documents issued in today’s environments, and in so doing, to have a high degree of confidence that the applicant is presenting a genuine identity.
Our partnership with L1 Identity Solutions, the manufacturer of the B5000 identity document scanner, allows us to offer our financial institution customers a set of solutions that can simplify the identity authentication process and which can be seamlessly integrated into existing business processes using best practice implementation. L1 is the manufacturer of the ID documents for the majority of North American jurisdictions, and thus, are able to authenticate the ID documents based upon their knowledge of what has been built into these documents for authentication purposes.