counterfeit detection
How to Spot Counterfeit Cash and Protect Your Business If you run a business—or even just handle...
Why Omnichannel Fraud Is a Growing Concern Today’s customers interact with auto dealerships and...
Counterfeits Just Keep Getting Better In 2023, a retail store in California unknowingly accepted...
To ensure your FraudFighter equipment remains effective and reliable, routine maintenance is...
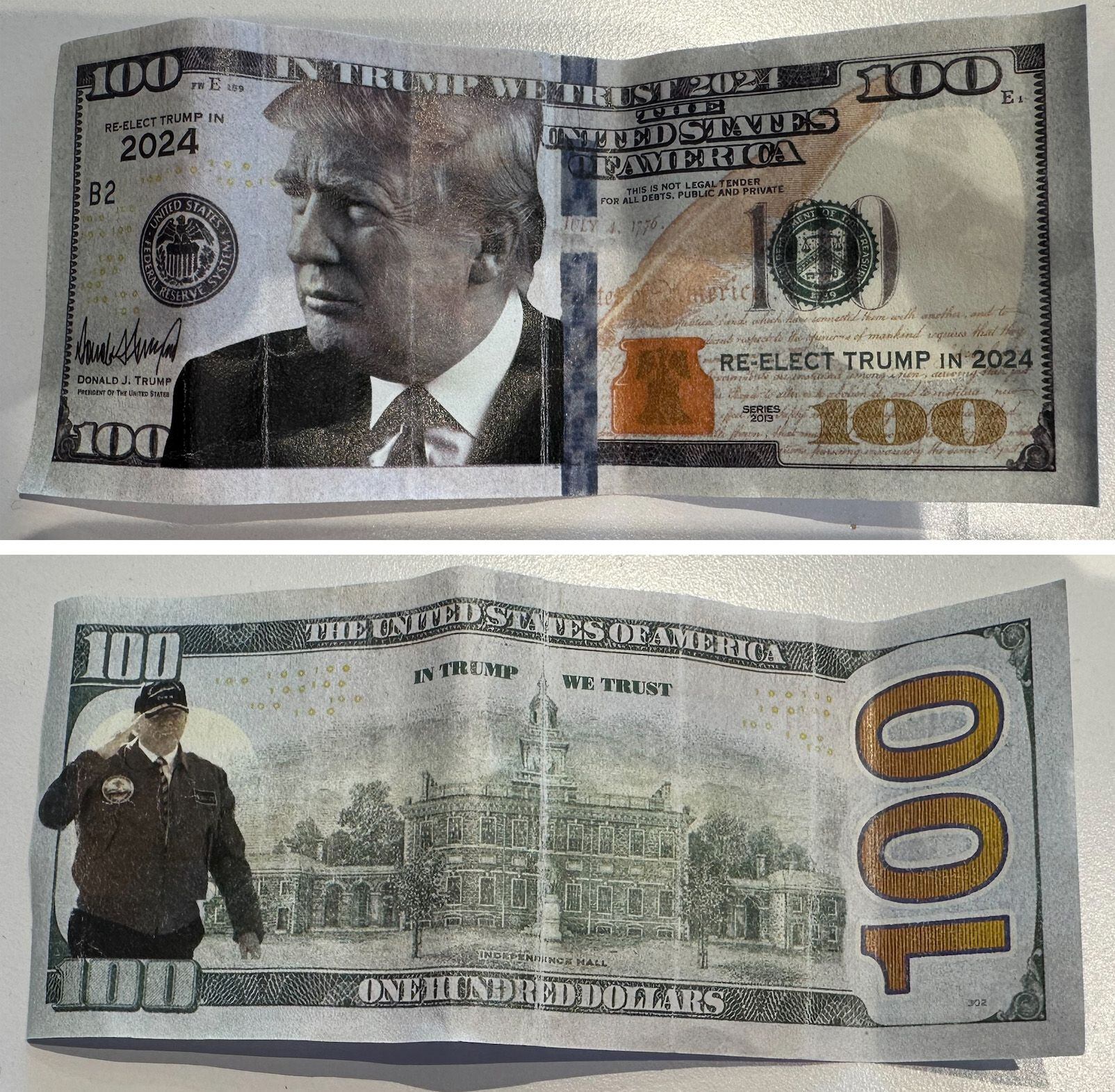
Over the past few months, we’ve witnessed a troubling resurgence in ultra-quality counterfeit...
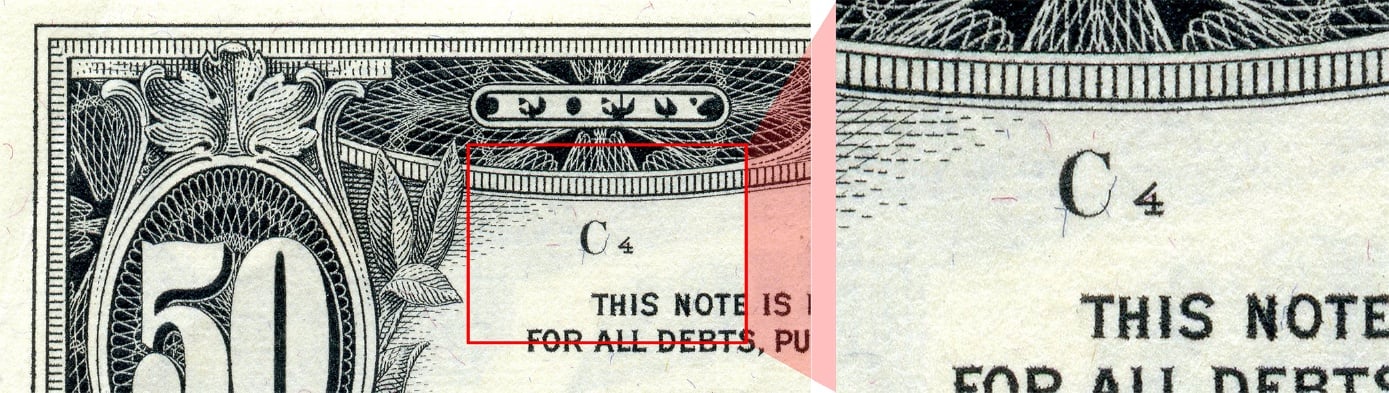
The scenario: A fraudster acquires large amounts of real $1 bills. He then goes through the process...
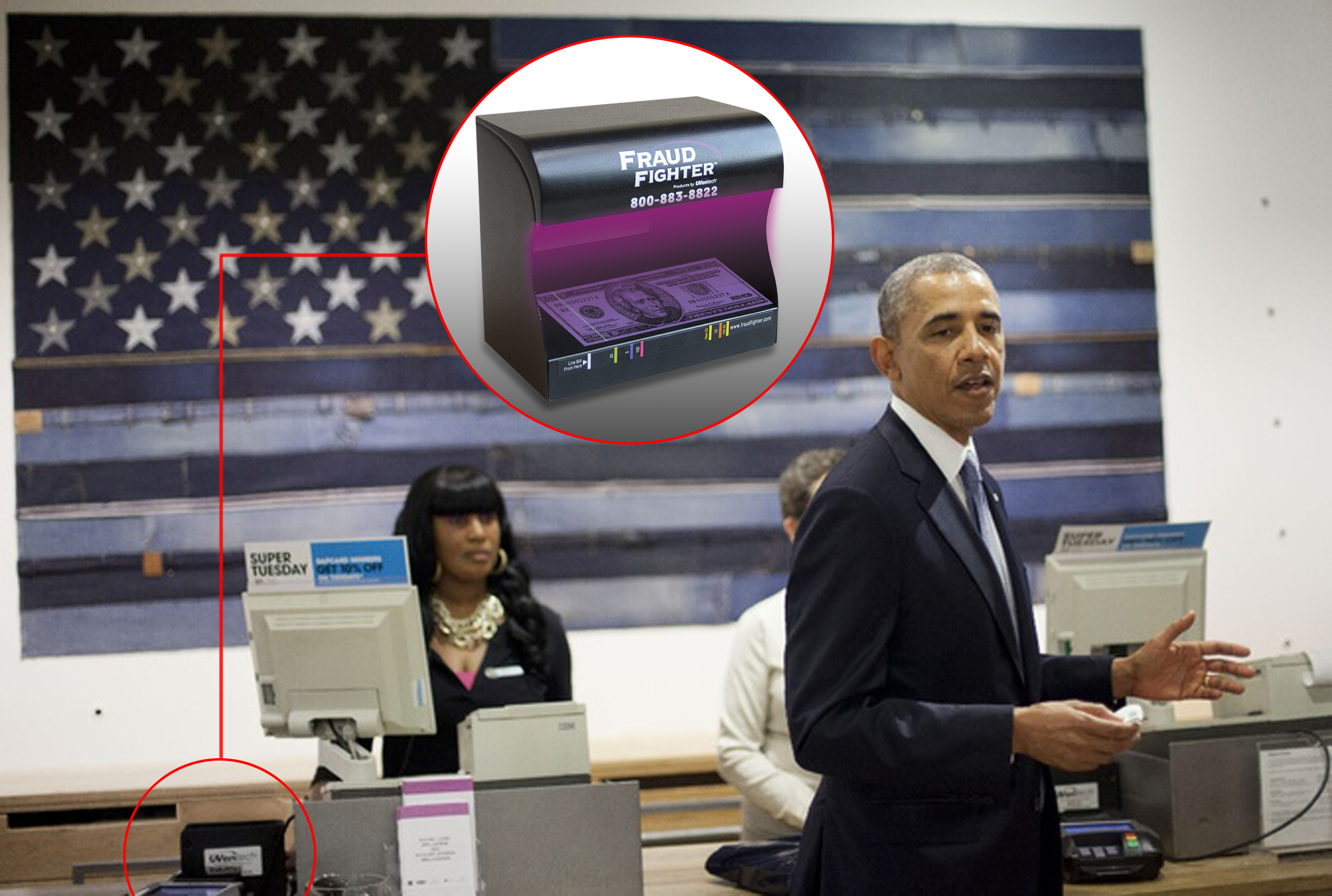
Counterfeit detection continues to be one of the most crucial steps a brick-n-mortar operation can...
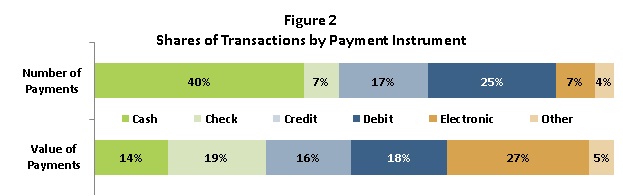
Enter 2022. The technological landscape is ever evolving and with it, payment methods. More and...
You detected counterfeit bills in the back office? Great! But it’s too late…
What to do when they win! ID authentication should be a fundamental step anytime a “qualifying...
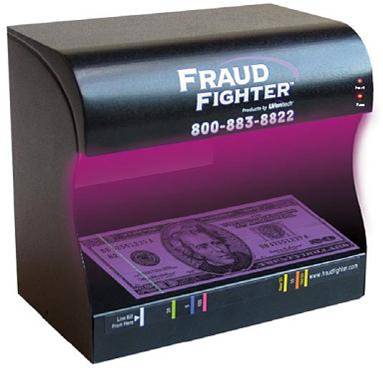
There is a surprising range of counterfeit detector options available in the marketplace today....
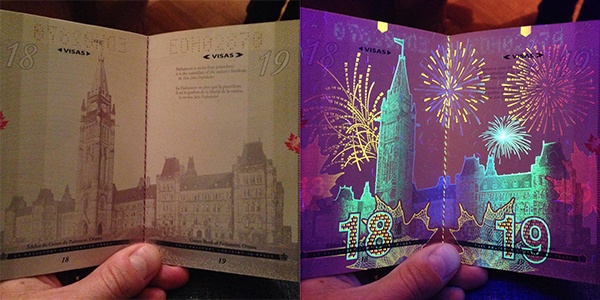
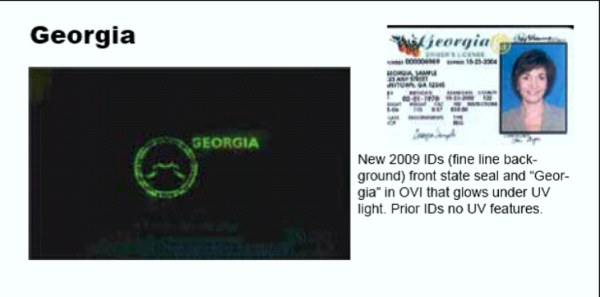
Countries around the world are designing ever-more intricate (and beautiful!) UV security features...
Employees tasked with running cash registers and point of sale (POS) systems are a store’s first...
As of this writing in early March 2021, COVID19 vaccine deployments have given society a proverbial...
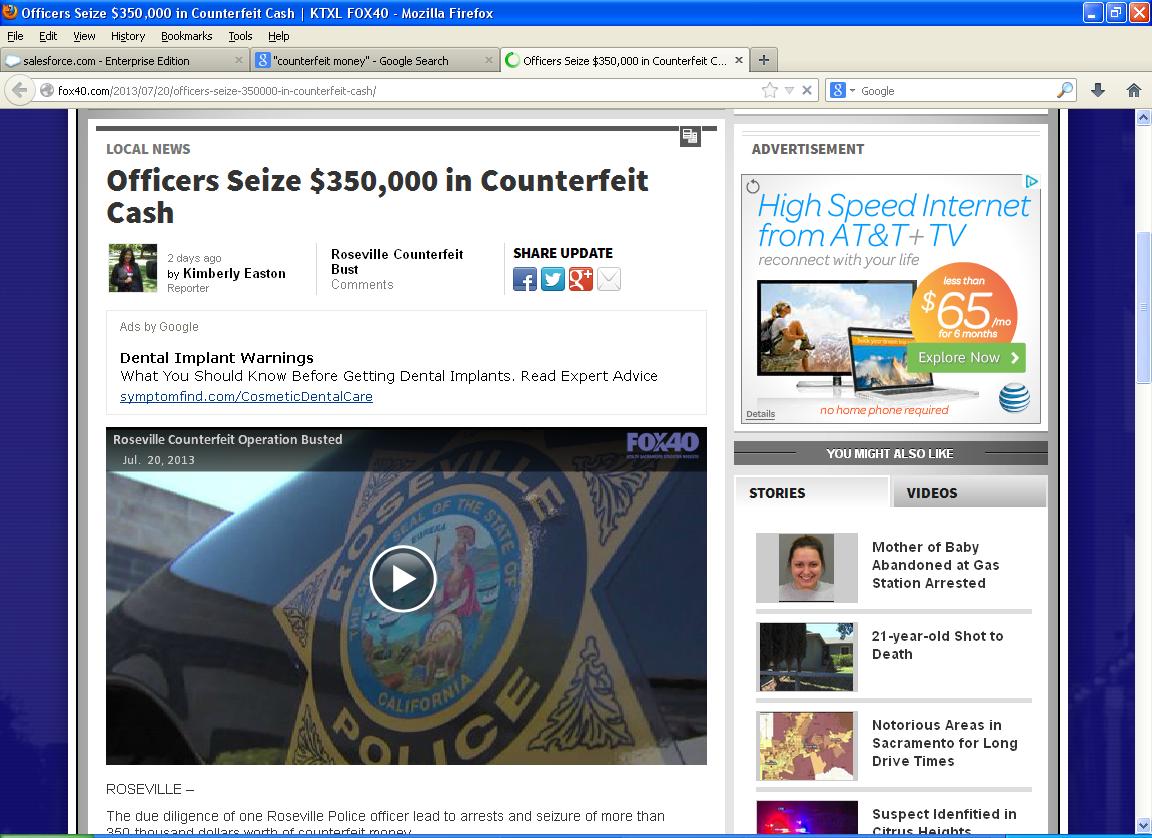
A quick perusal of recent news stories using the keyword “counterfeit money” reveals the most...
Two Packages, $136K of Counterfeit Currency CBP Officers in Chicago Seize Shipments Containing...
When it comes to assessing your risk of identity theft and fraud, being digitally compromised in a...
Several weeks ago, we began getting calls from a few clients asking us whether specific versions of...
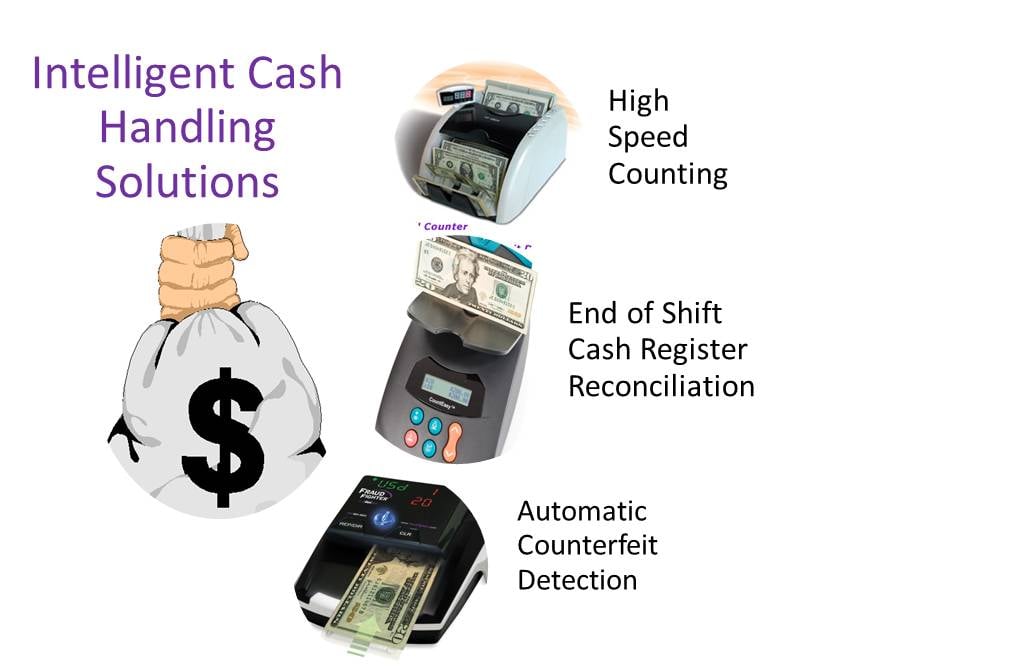
Increase Your Employees’ Productivity by Eliminating the Time-Consuming Task of Counting Money
• TABLE OF CONTENTS •Equifax Hack: The FactsHow Criminals Can Use This Stolen DataIdentity...
Image of a Series 1928 Federal Reserve Note • TABLE OF CONTENTS •A Brief Background on U.S....
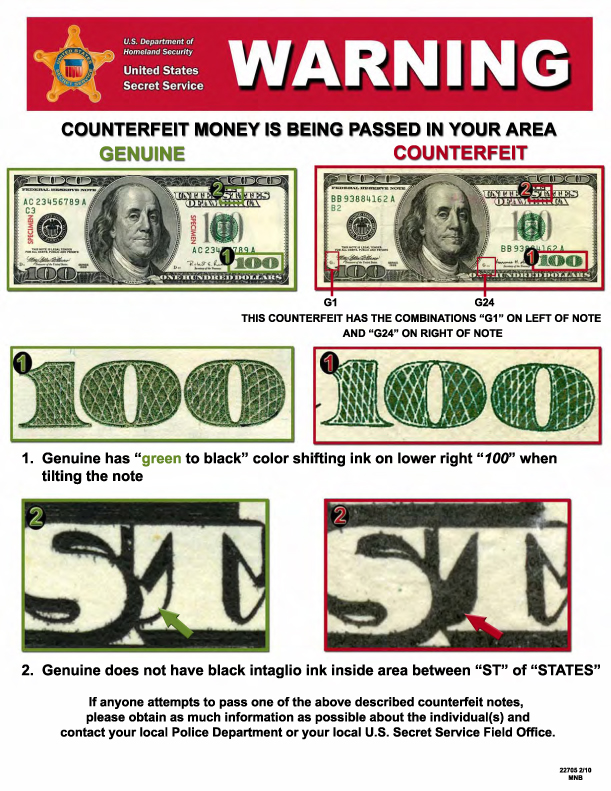
• TABLE OF CONTENTS •Why You Need to be Vigilant about Checking MoneyNaked Eye vs. Counterfeit...
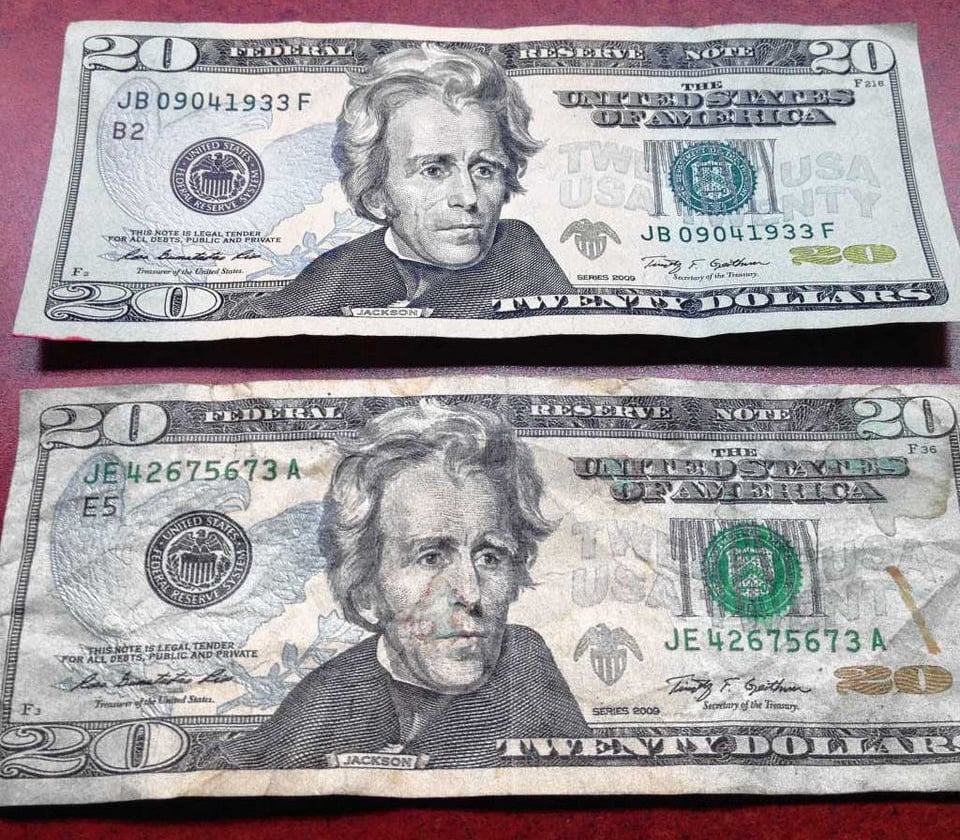
Can you tell which twenty is fake? The twenty on top is real and the twenty on the bottom is...
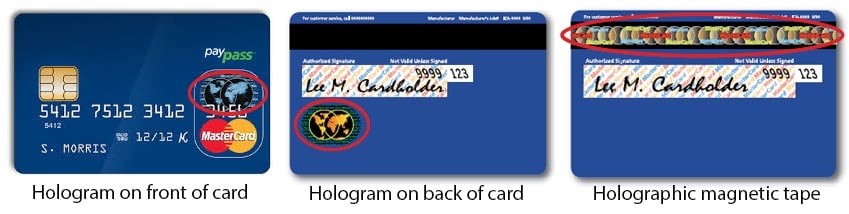
In the previous post, we discussed what EMV and the fraud liability shift are as well as how it...
Most people have some exposure to fraud deterrents in their daily lives. For the honest person,...
According to a new report, the majority of online fraud in the United States is coming from several...
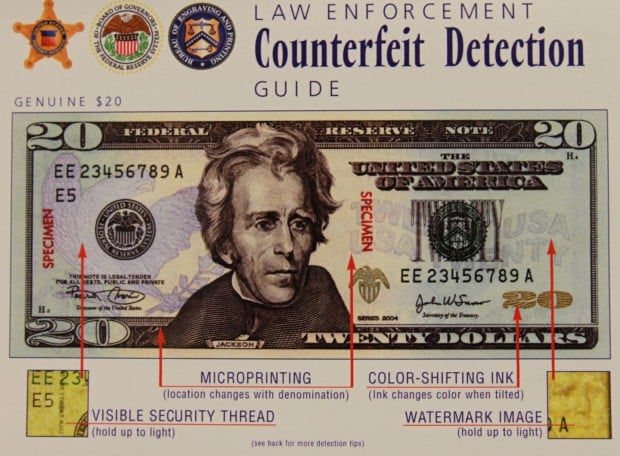
Modern counterfeit detection relies on a wide range of specialized detectors, but there is a...
Scientists out of the National University of Singapore have found a method of utilizing nanohole...
Identity theft and fraud among senior citizens is rising across the country, with many states as...
Counterfeit money has been around as long as authentic money. Even some of the very first western...
Counterfeiting and identity theft are major concerns for the public, and safety of private...
For as long as governing bodies have released official documents and notes, counterfeiting has been...
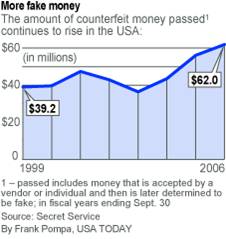
Counterfeit money damages the U.S. economy and can substantially impact businesses of all...
The modern era of counterfeit money production has enabled anyone with a home computer, a scanner...
In 2013, the U.S. government says it recovered more than $88 million in counterfeit currency in the...
Recently, a news story was featured on CBS 2 News Cedar Rapids, Iowa, that highlights the...
Does your business handle in-store credit applications? Are you verifying the identifications of...
The holiday season is nearing meaning the busiest time of the year for retail businesses is...
Black market websites, located in the “deep web” are known for supplying sophisticated criminals-...
It is a widely held belief these days that the end of the “cash economy” is upon us. With rapid...
Would You Have checked his $100 Bill for Counterfeit? When training your workers to detect and...
Reports Already Coming-In about the New $100 note "falling apart'
The United States has launched a new $100 bill as of October 8, 2013, the first remake of the...
New Report by Tufts University Details Costs of Cash-Economy to both Businesses and Individuals I...
Yet Another Production Delay may Affect Release Date for New $100 Bill New Anti-Counterfeiting...
Every day, I get news clippings - courtesy of Google news - on the topic of counterfeit money. The...
The U.S. Treasury Department's Bureau of Engraving and Printing (BEP) announced that the...
Over the past 14 months, the Bank of Canada has released a series of newly designed banknotes. The...
I really can't give the Federal Reserve or the Bureau of Engraving and Printing a hard time. The...
I read an interesting Article yesterday on Motley Fool, one of the sites where I go for relevant...
Fraud and data security breaches come in so many different forms and from so many different...
Halloween is over and the holiday season is upon us. This means retailers should expect large...
Peru Supplies 1/3 of all Counterfeits in U.S. Last month Peruvian authorities, in conjunction with...
Knowing how to spot fake money is a skill that every cash handler should know. With advances in...
Many of our customers ask us - Why is the UV security feature on the $100 bill more difficult to...
As technology advances and as more people become aware of the simplicity of digital
If Internet conversation is any indication, businesses and consumers continue to harbor fears of...
Companies lose billions of dollars every year to counterfeiters who are clever enough to print...
"Get Money" isn't just a song by The Notorious B.I.G.
Manually counting cash is one of the best ways to lose money in your retail business. Cash...
In 2009 the U.S. Treasury reported that over $400 Million in counterfeit currency was...
For as long as people have used paper currency, there have been attempts to counterfeit it. In...
The best way to detect a counterfeit bill often depends on the context, such as the type of...
Most people associate the United States Secret Service with the protection of the President and...
Counterfeit currency. Not something most of us think about. We think we know what it is and some...
Loss. Whether it happens in the form of shoplifting, cash register shortages, product shrinkage...
In today's economy, organization - from "mom and pop" stores to giant retailers - are looking for...
Desktop publishing to make money: A simple business concept used either to supplement income or...
Judging by the number of Google searches devoted to it, counterfeit money continues to be a big...
Counterfeit money. According to the United States Secret Service, $261 million in counterfeit...
In the past, fake ID’s have largely been associated with underage drinkers trying to get their...
I n the ongoing war against identity theft, individual battles are constantly being waged and...
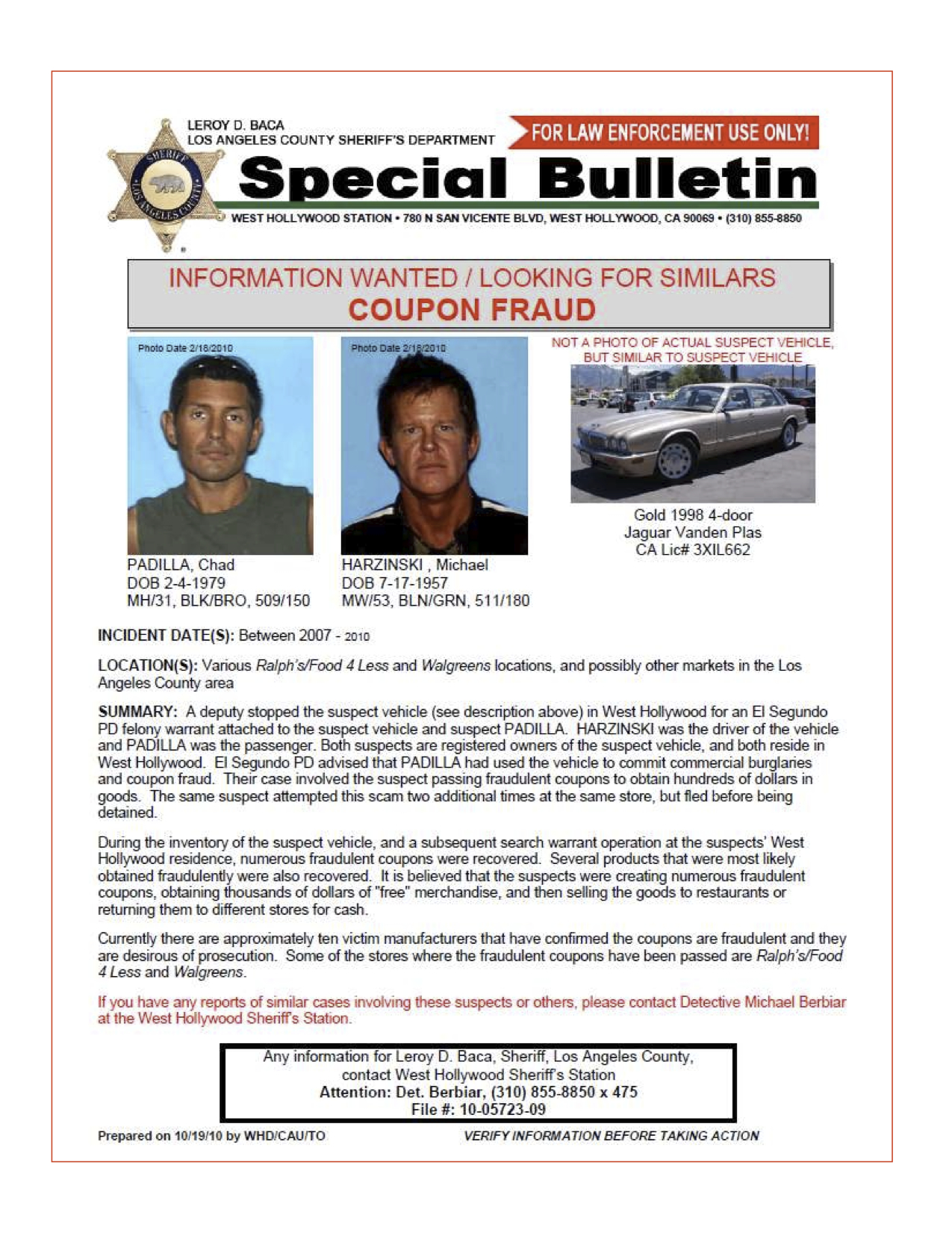
“Extremely troubling,” is how one Arizona public safety officer described the small items in front...
Criminals interpreted the American prospect of “making money” quite literally in the past month,...
Earlier this month, FraudFighter began providing advanced sample copies of our new Driver License...
Credit card processing servers. Poorly secured corporate networks. Point-of-sale terminals in gas...
We have mentioned in a number of previous posts the international nature of many counterfeit money...
(Note: This is the second article in our series Best Practices for Counterfeit Detection. For the...
Want an entertaining dinner party activity? Ask people around the table if they know how to tell...