regulatory compliance
Starting April 1, 2026, FINTRAC (Financial Transactions and Reports Analysis Centre of Canada) is...
What is a Notary Public?
As of this writing in June 2021, fraud and cyber crimes are running rampant and unabated throughout...
As of this writing in early March 2021, COVID19 vaccine deployments have given society a proverbial...
If you are in noncompliance with Form I-9 requirements, your business could pay a rather hefty...
Despite the Securities and Exchange Commission's focus upon regulating the securities industry and...
This article was originally published on CBinsight.com The Best Way to really "Know Your...
Bank Secrecy Act compliance is more important than ever to companies that deal with “covered...
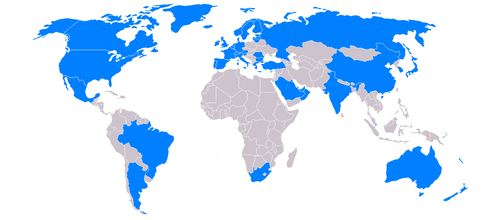
To deter or prevent illegal activity including terrorism and money laundering, Bank Secrecy Act...
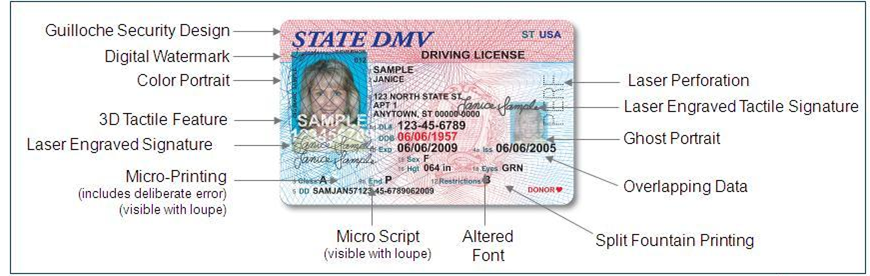
At the heart of many acts of fraud lies the intentional misrepresentation of identity. When ORC...
The world has changed much since September 11, 2001. Awareness of how fragile our way of life can...
If you have followed the news at all lately, you have likely heard that financial institutions of...
It is perhaps a sign of the times when the annual convention of anti-money laundering...
Scenario:A financial institution is opening a new branch, and is starting a major local PR blitz...
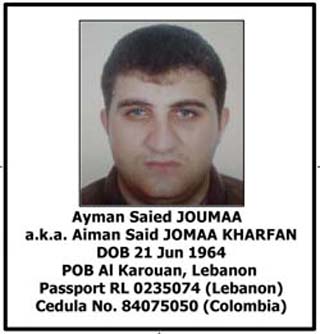
The last several weeks have seen a number of noteworthy arrests for money laundering. A fugitive...
The last decade brought about a tumultuous change in financial institution regulations. Many...
As if it weren’t already difficult enough to verify identity documents, now comes a new wrinkle in...
Credit card processing servers. Poorly secured corporate networks. Point-of-sale terminals in gas...
Mortgage fraud has been much in the news in recent years. After the dust created by the...
There’s a lot of semantic debate these days over what to name foreign nationals who violate U.S....
In a startling revelation yesterday, one of the largest U.S. banks admitted in court that a...
Burden, or Benefit?
Part 4 of a four-part Process for Setting-up a Red Flag Rules Compliance Policy UPDATING THE...
If your organization is involved in the financial services industry, or in any way has a regular...
This is the first in a series of articles discussing the challenges faced by casinos - regarding...
Part II of a Four-Part Procedure for Compliance with Identity Theft Prevention Requirements If your...
Part I of a Four-Part Procedure for Compliance with Identity Theft Prevention Requirements
NRF Loss Prevention Blog Article In a very interesting blog article found an the National Retail...



.png)