card not present fraud
“Buy online, pickup in store” (BOPIS) has become ubiquitous. According to an article by Digital...
How "Know-Your-Customer" (KYC) can be a Jackpot for the Online Gaming industry
One of the most vital questions that confront managers of public-facing operations today concerns...
As of this writing in early March 2021, COVID19 vaccine deployments have given society a proverbial...
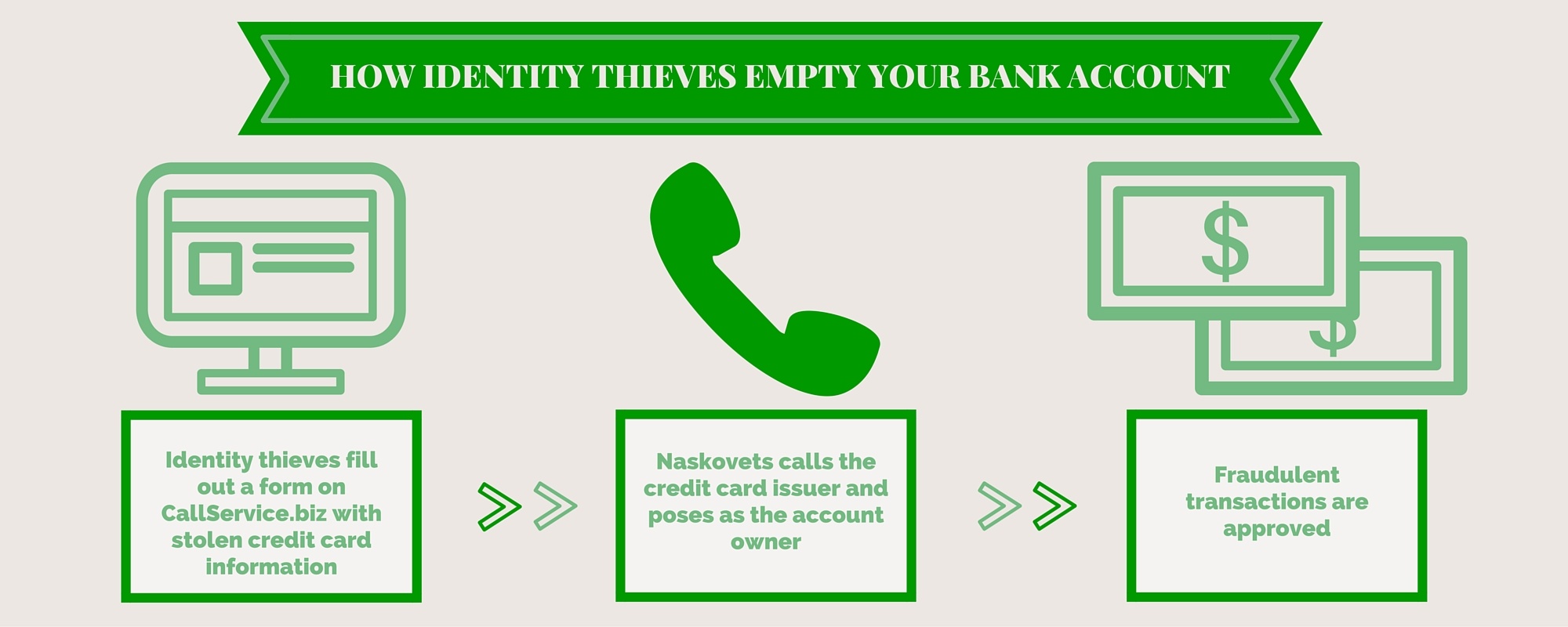
• TABLE OF CONTENTS •Equifax Hack: The FactsHow Criminals Can Use This Stolen DataIdentity...
Retailers are on course to lose more than $70 billion globally to remote “card-not present” (CNP)...
• TABLE OF CONTENTS •CNP FraudIdentity Fraud via Phishing, Malware, and Social MediaOther Identity...
• TABLE OF CONTENTS •What is Return Fraud?Return Fraud StatisticsWhy is Return Fraud such a Problem?
• TABLE OF CONTENTS •Consumer Behavior during the HolidaysHoliday 2015 Retail Stats ReviewHoliday...
If you’ve been paying attention to the news, you’ve probably noticed something: the rapid rise of...
For most, the start of a new year is a time to reflect on goals and positive changes. It is when...
For many years, credit card fraud has been the favored method for fraudsters seeking to profit from...
It was only a decade ago that we lived in a 4G-less world – at an intersection of equal parts...
In short, yes, you should be worried – but not too much.
Like most millennials, if you left college tens of thousands of dollars in debt with looming...