
The Next Big Wave of Fraud: Card Shimming
• TABLE OF CONTENTS •
What is Card Shimming?
Card Shimming vs. Card Skimming
What are CVVs?
Why Cards are Skimmed
Why Cards are Shimmed
Why Card Shimming is a Bigger Problem than Card Skimming
How to Protect Yourself from Card Shimming
According to FICO, the number of compromised ATMs rose by 546% from 2014 to 2015 thanks to the popularity of card skimming.
Adding to the worrisome popularity of card skimming, more and more cases of card shimming have been popping up across the globe.
What is Card Shimming?
You know how virtually all debit and credit cards out there these days have microchips in them and how more and more payment terminals at stores have you inserting your debit/credit card as opposed to swiping? That’s because the microchip is supposed to prevent debit/credit card fraud.
Enter card shimming.
Criminals have figured out a way to capture data from that microchip and use it to make fraudulent transactions via card shimming. And, alarmingly, more and more reports are coming in that card shimmers are being discovered around the world.
Fortunately, it seems as though card shimming is nowhere near the epidemic card skimming has become, but it is quite perturbing that criminals have found a way to exploit the microchip in such a way that negates the entire reason why cards with microchips are considered more secure.
Card Skimming vs. Card Shimming
Put simply, card skimming is the act of illegally capturing data off the magnetic stripe on that is found on the backs of all debit and credit cards.
Card shimming, on the other hand, is the act of illegally capturing data found on the microchips of EMV-compliant debit and credit cards, aka smart or chip cards.
In order to explain the differences between card skimming and card shimming as well as why both types of fraudulent activities were invented in the first place, CVVs need to be discussed.
What are CVVs?
The CVV, or the card verification value, is a security measure placed on debit and credit cards in order to reduce fraud. It is sometimes referred to as the CVC, or the card verification code. For simplicity’s sake, from here on out, usage of ‘CVV’ also implies ‘CVC’; in other words, just ‘CVV’ will be used to refer to both ‘CVV’ and ‘CVC’.
On cards without microchips, there are two CVVs: the CVV1 and the CVV2. On cards with microchips, there are three CVVs: the CCV1, the CVV2, and the CVV3.
The CVV1 is encoded onto the magnetic stripe on the backs of debit and credit cards and has the purpose of preventing fraudulent card-present, or in-person, transactions. A correct CVV1, in theory, is assurance that the person conducting the transaction is the true owner of the card, and not a criminal who has made a counterfeit card using someone else’s debit/credit card number.
The CVV2 is the three-digit number printed on the backs of debit and credit cards – or the four-digit number printed on the front of American Express-branded debit and credit cards – and has the purpose of preventing fraudulent card-not-present (CNP), or online or over-the-phone, transactions. A correct CVV2, in theory, is assurance that the person conducting the transaction is the true owner of the card, and not a criminal who has simply memorized/copied the card number from someone else’s debit or credit card.
The CVV3 is encoded onto the microchip on EMV-compliant debit and credit cards – more on EMV below (add anchor link) and is designed to prevent in-person counterfeit debit and credit card fraud. The CVV3 changes for each transaction – only the card issuer and the card itself should be privy to what the code should be for any given in-person transaction. By having the technology in place to make sure that this code is the correct one for each and every transaction, the theory is that fraud can be prevented.
Note: CVV3 is often referred to as the iCVV, or the integrated circuit card verification value.
Why are Cards Skimmed?
At the beginning, debit/credit cards only had the magnetic stripe on the card.
For criminals to use these cards fraudulently, they had two choices:
- steal the card, or
- obtain the data from the magnetic stripe and create a counterfeit card
Although the first choice may seem easier, the second a victim reports his/her card stolen, the stolen card becomes useless - which is why more and more criminals opted for the second choice.
The second choice’s hurdle was discreetly obtaining this data such that the true card owner would not notice that his card data has been compromised – the longer the owner doesn’t know, the longer the criminal can siphon funds from the card. The solution criminals came up with was to design and manufacture a device – the card skimmer - that can capture and record the data from magnetic stripes at the places they are used: at point-of-sales (POS) terminals and at ATMs.
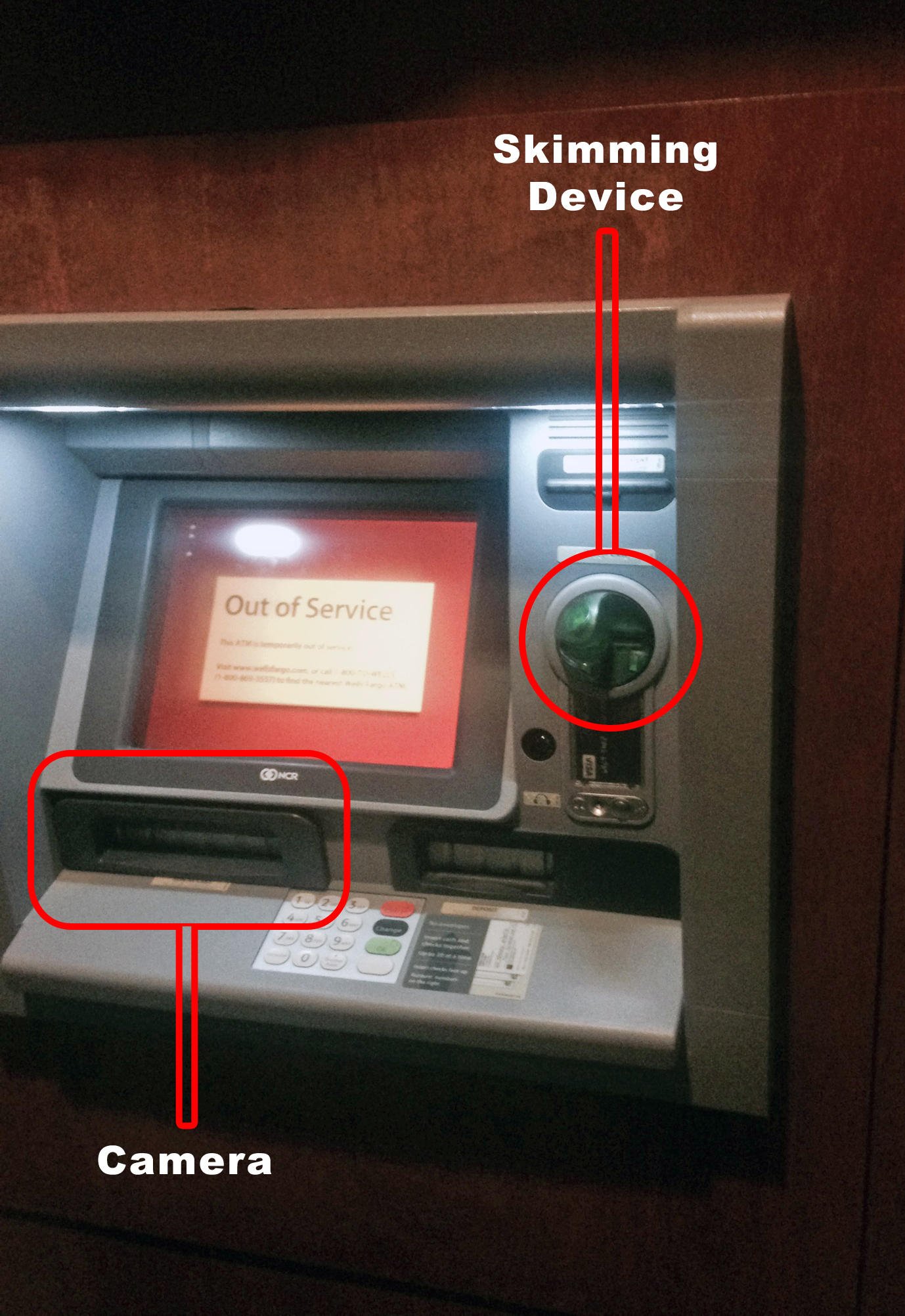
Card skimmers are discreet devices that sit either on or in card swipe reader on POS terminals and ATMs so that whenever a card is swiped through the reader, the data on the magnetic stripe can be captured and recorded.

To get a more in-depth overview of card skimming, check out our Card Skimmng 101 post.
The magnetic stripe on the back of a debit or credit card contains data about the card and its owner along with the CVV1. This data on the magnetic stripe is written in plain text, which allows skimming devices to record the data that is on the magnetic stripe.
Once criminals obtain this data, they create a counterfeit debit/credit card. And just how are counterfeit debit/credit cards created? By purchasing legal, readily-available blank cards on the Internet for as little as $0.15 per card.
To be clear, there are actually many legitimate reasons to purchase blank credit cards - such as using them to provide efficient identification of customers/employees/etc. for businesses - which is why these items are allowed to be sold and purchased online. By encoding and embossing stolen debit/credit card data onto these blank cards, criminals can use those counterfeit cards to make fraudulent purchases.
Simply memorizing a set of debit/credit card numbers and embossing that number and encoding the visual data – but not the CVV1 – onto the magnetic stripe will result in a failed transaction every time, which is why the data on the magnetic stripe needs to be captured.
When attempting to use counterfeit cards in-person at a store, criminals can run into one final hurdle: the cashier asking for identification. To use these counterfeit cards in-person, criminals then have to procure counterfeit identification, such as a driver’s license, to accompany the counterfeit card.
Although the costs of obtaining blank identity documents, such as driver’s licenses, are similar to those of obtaining a blank payment card, detecting counterfeit identification documents by physically inspecting the document is much easier and obvious than physically detecting whether or not payment cards are counterfeit. This is due to the fact all government-issued identity documents have many more security features than debit/credit cards.
With the need for proper identification for in-person purchases, criminals naturally began to move towards an arena where identification was not a factor: the Internet. For purchases made online, criminals simply needed to input the stolen debit/credit card data without proving their identities.
This, of course, didn’t mean that criminals simply stopped attempting to make fraudulent in-person transactions – what this meant was that fraud became a much more lucrative endeavor, attracting more and more people to the world of fraud via stolen debit/credit card data. In short, the world of card fraud grew exponentially.
Thus, the magnetic strip and the data on it are simultaneously a necessity and a vulnerability.
The magnetic strip and its data are necessary, obviously, to conduct legitimate transactions: the data is read by the card processor to make sure that the correct person’s account is being charged and that he or she has the needed funds to pay for the transaction.
The magnetic strip and its data are vulnerable because of the fact that it simply exists on the card; basically, if the data didn’t exist on the card, how would criminals be able to get their hands on it?
If there’s data, the fraudsters will come.
Why Cards are Shimmed?
To put a stop to card fraud, particularly in the online environment, the CVV2 was added. By making sure that the correct CVV2 was entered for online transactions, businesses could be much more confident than the pre-CVV2 days that the person conducting the transaction is the true owner of the card. In essence, the only form of online card fraud would stem from stolen cards as opposed to counterfeit cards.
Since the CVV2 is not encoded onto the magnetic stripe, criminals were discovering that less and less online transactions could be conducted successfully, which led them to back to old-fashioned in-person card fraud.
It should be mentioned that criminals also found a new way to conduct card fraud using the CVV2: keyloggers. Almost every day these days, there is news about a new malware affecting computers. While not all malware is designed to log keystrokes, there are a good number out there whose purpose is to do just that.
On an infected computer, when someone enters their credit card information – including the CVV2 – in order to make a legitimate transaction, the malware will record the keys that are typed in and send the data to criminals, and by deciphering the key strokes, the criminals can ascertain the CVV2.
Of course, malware - especially effective, inconspicuous malware – requires a certain level of technical mastery, which leaves most card fraudsters to turn to more traditional methods of card fraud.
The addition of the CVV2, unsurprisingly, didn’t lead to much of a decrease in card fraud – criminals simply found another path of least resistance from which to profit.
And so, financial institutions banded together to create a standardized way to protect the data stored on debit and credit cards in such a way that in-person card fraud could be virtually prevented: with a microchip.
The financial institutions that came together to create this chip standard are collectively known as “EMV”, which stands for “Europay, Mastercard, and Visa”; more financial institutions, such as American Express and Discover, have since joined, prompting a nominal change from “EMV” to “EMVCo”.
The addition of these institutions is why virtually all debit and credit cards are slowly but surely converting to chip-enabled cards. And why so many stores are slowly but surely enabling their POS terminals to accept transactions using chip-enabled cards.
If you’d like to learn more about EMV, its changes to debit/credit cards, and how it affects you/your business, please read our post about EMV.
But, in order to understand the difference between card skimming and card shimming, you don’t need to know everything about EMV or its changes – what you need to know is that:
- the microchip stores the CVV3
- POS terminals that are EMV-compliant are designed to detect for the presence of the chip, and that,
- if the chip is present, that the terminal will require the card to be inserted so that the microchip can be read as opposed to swiped so that the magnetic stripe can be read
The CVV3, unlike the CVV1 and CVV2, is not static, meaning that it changes with each transaction. The information that is encoded onto a magnetic strip of chip-enabled cards contains code that communicates to POS terminals that the card has a chip and thus needs to be inserted so that the microchip can be read.
Copying and pasting the data from magnetic stripes on these cards onto counterfeit cards does not allow for successful transactions – encoding this data onto a counterfeit card will simply prompt POS terminals to ask for the card to be inserted so that the microchip can be read and if there’s no microchip? The transaction does not go through.
In theory, the correct CVV3 for any given transaction is known only by the card issuer and the microchip on the card. The correct CVV3, in essence, means that the real card, not a counterfeit one, is being used to make the transaction – unless, of course, the card was simply stolen (which is why it is important to require I.D. for credit card transactions!)
With the introduction of the CVV3, it may seem that there is no value in capturing data off of debit/credit cards since:
- less and less online transactions can be done successfully without knowledge of the CVV2
- the CVV3 has essentially rendered in-person card fraud useless since the unknowable CVV3 needs to be known for each transaction
And here, finally, is where card shimming comes into play.
The technology behind EMV, its microchips, and how it processes its payments, unfortunately, is not as foolproof as we’d like to believe.
EMV has been implemented in the United States for less than two years and already criminals have found a flaw in the way EMV technology works – verifying the CVV3 – and card shimmers are used to take advantage of this flaw.
Card shimmers function much like card skimmers in that their purpose is to read and collect the data found on debit/credit cards, but, as said above, reads the microchip instead of the barcode.
Card shimmers are placed within POS terminals and ATMs so that whenever a chip-enabled card is inserted, the data from the microchip can be obtained. The port in which a credit card needs to be inserted is extremely thin – just barely tall enough to accommodate credit cards. In order to successfully manage to read the microchip and sit inside the terminal undetected, a card shimmer device would have to be no more than 0.1mm tall.
It may seem somewhat absurd that anyone can create anything that is thin enough to insert into the chip reader considering how thin a credit card is; to put it into perspective, the average human hair is just 0.18mm thick. But, unsurprisingly, enterprising criminals have figured out a way to manufacture a device that is thin enough to encapsulate the credit card within the chip reader.
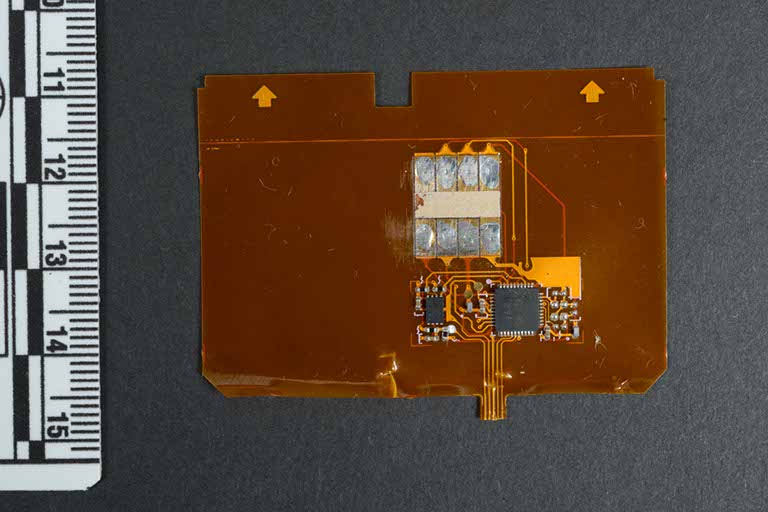
Criminals have figured out a way to manipulate the data found on the microchip in such a way that a counterfeit credit card that is tricked into relaying the message to POS terminals that the card is a non-chip-enabled card, allowing a swipe-based transaction to successfully go though.
In essence, card shimming allows criminals to bypass the protections provided by the CVV3.
Thankfully, at least, card shimming isn’t as popular as card skimming by any means, but that could be explained by the fact that the technology needed to make card shimmers are much more advanced.
If all of this isn’t unsettling enough, there are reports that, even from a card skimmer, the magnetic stripe data from chip-enabled cards can be manipulated in such a way that POS terminals do not recognize that data being from a chip-enabled card. This lets the data from a chip-enabled card to be used as though it’s from a non-chip-enabled card, re-opening the doorway for in-person card fraud to become popular again.
Why Card Shimming is a Much Bigger Problem than Card Skimming
Because card shimming is nowhere near the epidemic that card skimming is – although that’s not saying that it can’t ever be – it may be hard to see why card shimming is a much bigger problem than card skimming.
If, or should I say, when, card shimming becomes a more popular criminal endeavor, it will become more and more obvious that all the resources and time poured into EMV and its technological ‘upgrades’ will have been for naught.
After all this EMV-related fiasco, we may still end up back at square one when it comes to combatting card fraud if card shimmers become just as popular as card fraud.
How to Protect Yourself from Card Shimming
Unlike card skimmers, which are bulkier and tend to be more obvious, card skimmers are much harder to detect without dismantling POS terminals and ATMs.
However, there are certain steps you can take to prevent, or, at least, mitigate the effects of, card fraud.
- Use cash, if you can
- Keep an eye on your bank/credit card statement as much as possible for any unauthorized charges
- Try not to use standalone ATMs, such as those found in convenience stores, as they are not as well-maintained or secured as bank ATMs
- When at the ATM, cover the PIN pad with your hand as you type in your PIN. While this may not prevent your card data from being collected and used at POS terminals, criminals cannot directly empty your bank account since they do not have your PIN





.png)