
Traditionally, “skimming” meant secretly taking small amounts of money from a larger amount of money, such as taking a couple of dollars from the cash register when the boss wasn’t looking. But today, skimming colloquially refers to card skimming.
Card skimming is the act of illegally capturing debit/credit card information during an otherwise legitimate transaction, such as making a purchase at a store or taking out money from an ATM. The goal of card skimming activities is to use the stolen debit/credit card information to commit fraud in the cardholder’s name.
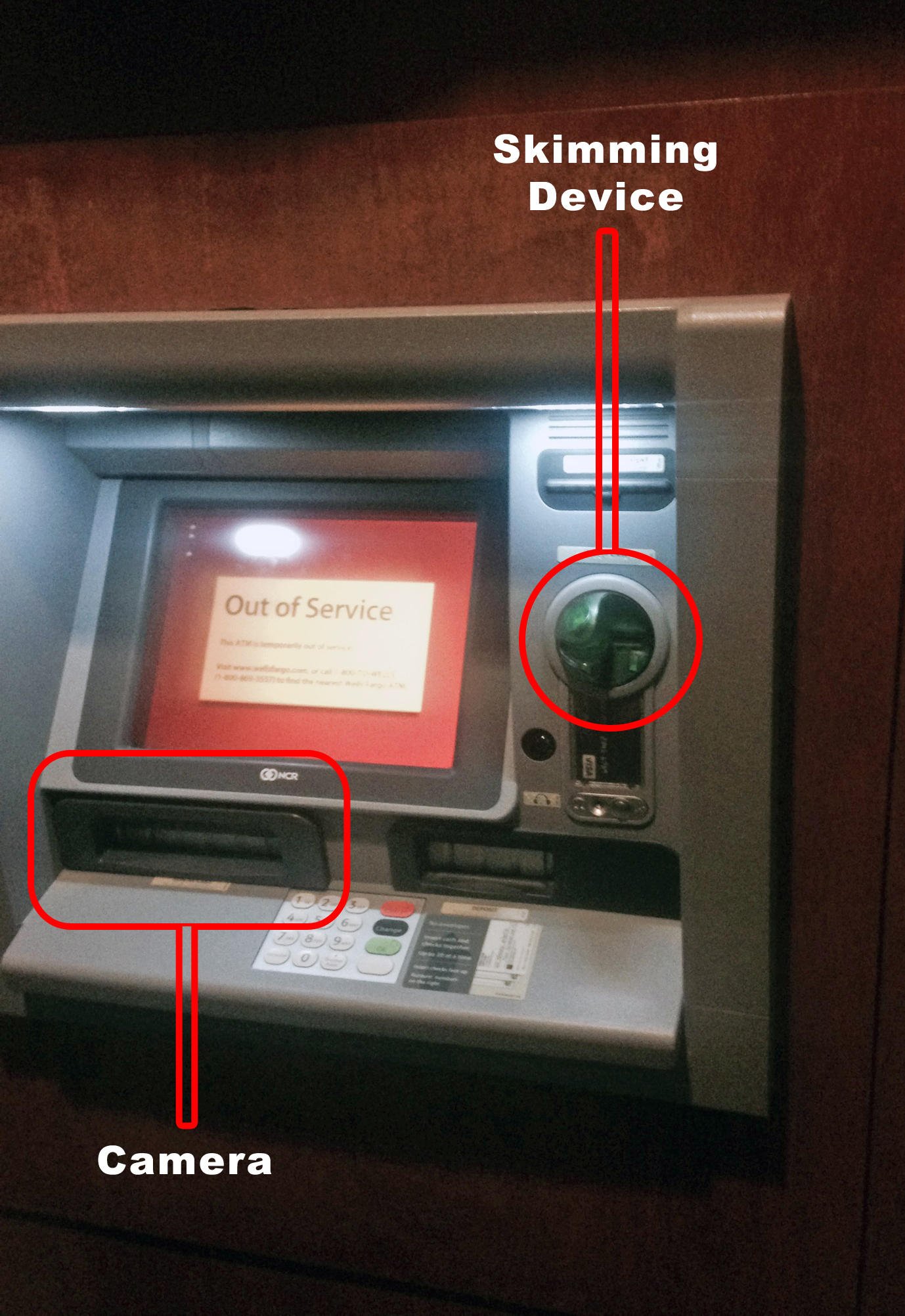
Card skimming occurs in one of two places: at or near point-of-sale payment terminals or at ATMs. In order to capture debit/credit card data, criminals use a small electronic device known as a ‘skimmer’ that is capable of recording the data embedded on the magnetic strips of debit/credit cards as they are swiped in a payment terminal or ATM. The skimmer is placed as either an overlay that is identical or blends in with the legitimate terminal or ATM interface or hidden within the card reader of the terminal or ATM.
Skimmers usually record and store payment card data internally, which means that criminals will need to return to the scene of the crime in order to complete their scam. However, more and more card skimmers have been found to be taking advantage of wireless and Bluetooth technology – they can collect the card information from a discreet location whenever they want.
“Today’s world of skimming is high-tech, and it wants your credit card and banking info.
ATM skimming, credit card skimming, and their consequences are all discussed in more detail below.
ATM Skimming
According to a report released by FICO earlier this year, ATM compromises in the US rose 546% from 2014 to 2015. The number of ATM compromises in 2015 was the highest ever recorded.
Since the only type of payment card used at ATMs is the debit card, criminals need to take an extra step to skim cards at ATMs: they need to be able to capture the PIN as well to maximize their illicit profits.
Although criminals can potentially use debit cards without a PIN to make purchases, criminals who conduct ATM skimming usually do so in order to obtain information that can be used to siphon money directly from bank accounts. This is why virtually all ATM skimming operations use one more piece of equipment in addition to skimmers: equipment capable of capturing PINs as cardholders enter them.
“A skimmer in the ATM world usually features two important pieces of hardware: A micro camera positioned within eyesight of the keypad, and a magnetic card reading device that captures your card’s details. To ‘clone’ – duplicate – your card, this is all the info a would-be thief needs.”
There are two types of equipment that criminals can use to capture PINs: cameras and keypad overlays.


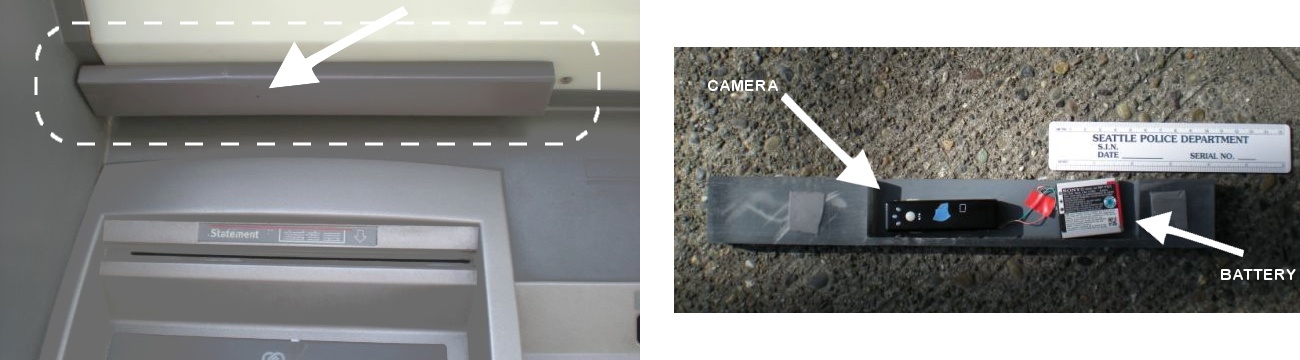
PIN-capturing cameras at ATMs are so small that they can be hidden quite easily in the ATM environment – in the brochure holder, mounted at the top of the ATM, or even can be placed within the card reader.
Keypad overlays, on the other hand, are pretty much what they sound like: a duplicate keypad to goes over the real keypad and records PINs as they are typed. The overlaid keypad is designed to look and feel as close to the real keypad as possible.
ATM skimming can occur at any kind of ATM - even ATMs found within banks, although very, very rarely. Non-bank ATMs, such as those found in convenience stores, are the most susceptible to skimming activities as they are not heavily monitored or serviced like bank-owned ATMs.
“From Jan. 1 to April 9, 2015, skimming at bank-owned ATMs increased 173.53% year over year, while growth at non-bank ATMs topped 316%, according to the 2015 FICO Card Alert Service. This type of theft accounts of billions in consumer losses.”
Credit Card Skimming
Credit card skimming occurs during transactions, at the point-of-sale, as mentioned above. What this means is that credit cards are skimmed via the machines that process transactions during a sale, such as the payment card reader at the register of a department store.
Unlike ATM skimming, capturing the PIN isn’t necessary for credit card skimming since credit cards cannot access the money in bank accounts. In most cases of credit card skimming, just the information on the credit card’s magnetic stripe is captured and recorded. Of course, criminals often opt to capture PINs as well since debit cards can and are often used in place of a credit card during a transaction.
Credit card skimming can happen anywhere a credit or debit card can be used to make a payment, such as a retail store:
“Skimming occurs most frequently at retail outlets that process credit card payments – particularly bars, restaurants, and gas stations”
As mentioned in the quote above, there are three types of transactions that credit card skimmer tend to target the most: restaurant transactions, bar transactions, and gas station pump transactions.
Restaurant transactions:
The reason why restaurant transactions are so popular for credit card skimming isn’t because restaurants use insecure point-of-sale terminals or something along those lines – it’s because of the method of paying at restaurants creates an opportunity that makes it hard for some employees to ignore.
At restaurants, especially at sit-down restaurants, customers who aren’t paying by cash hand over their credit or debit card at the end of the meal to their server who then processes the payment transaction. And this is when credit card skimming occurs.
Once out of view of the customer, criminally-enterprising waiters and waitresses quickly slide the payment card through a handheld skimmer, capturing and recording the card’s information. There have been cases where waiters/waitresses memorized or recorded the 3- or 4-digit CCV/CCV2 number on the back of the card to give the stolen information even more utility and value. Quick note: The CCV (“card verification value”) number is used to prove physical ownership of the card; CCV2 is the harder-to-guess second-generation improvement upon the original CCV and is found on most payment cards today.

Bar transactions:
It is pretty common for a customer to leave an open tab at a bar for the duration of time said customer is at the bar – an open tab allows for quick and easy ordering of the bar’s offerings. But to have an open tab, the customer almost always needs to leave behind either a credit or debit card with the server as a form of insurance. And this is where credit card skimming occurs in bars.
Much like the restaurant environment, bars provide a setting in which a server can skim a customer’s credit or debit card out of sight from the customer. After all, who keeps an eye on their credit/debit card that’s keeping an open tab the entire time?
Gas pump transactions:
Almost all gas stations have the option to pay at the pump via credit/debit card – no interaction with the cashier is needed. And this is where credit card skimming occurs at gas stations.
Criminals place overlays on the payment terminal that captures and records information from the magnetic stripe on cards as the card is swiped. Since some gas stations only allow payment via debit cards, skimmers at gas pumps are often accompanied by a camera or a keypad overlay to capture PINs as well.

Regardless of the location or type of transaction, credit card skimming can be perpetrated by either a criminal third party or an employee.
“Similar things happen with POS terminals in retail shops – payment registers – sometimes with the employee’s knowledge and sometimes without”
Although restaurants, bars, and gas stations are the most common places credit card skimming takes place, credit card skimming can take place anywhere debit/credit cards can be used as payment, even retail stores in which the payment card never fully leaves the presence of the customer.


The Profitability of Card Skimming
Exactly how do thieves profit from the debit/credit card information they collected via skimming? They sell it to other thieves or simply use the information themselves.
“When a credit or debit card is run through a skimmer, the device captures and stores all the details stored in the card’s magnetic strip. Thieves use the stolen data to make fraudulent charges either online or with a counterfeit credit card. In the case of ATM and debit cards, thieves withdraw cash from the linked checking account. The stolen card details may even be sold over the internet. Credit card skimmers are often placed over the card swipe mechanism on ATMs and gas stations. With ATMs, the crooks may place a small, undetectable camera nearby to record you entering your PIN.”
It’s somewhat ironic, but on the Internet, criminals have created an infrastructure that functions like normal, legitimate businesses – a marketplace where they can sell (illicit) goods and services to each other. In other words, other than the fact that the goods and services sold are illegal, the rest of the infrastructure behaves much like a regular marketplace.
One of the illegal goods that can be purchased online is a skimmer; ready-to-use skimmers can be purchased for as little as a couple of hundred dollars. To be clear, criminals can also purchase legitimate credit card readers that merchants use to conduct real sales and simply modify the reader to act as a skimmer.
Those who conduct card skimming operations with these card skimmers have two options: use the information they collected themselves or sell the information they collected to other criminals. Often, it is more enterprising (and less risky) to sell the information to other criminals.
Debit/credit card information is sold for as little as $5 or as much as $30 – depending on how complete the data is. For example, credit card information that also includes the three-digit CVV2 number found on the back of credit cards commands a higher purchase price than CVV2-less credit card information.
The criminals who purchase this information create counterfeit debit/credit cards to use for their gains. A quick search on eBay reveals that you can purchase black credit cards for as little as $0.07 per card.
So, for an investment of about $5 – or the equivalent of a large latte – a criminal can potentially have at their disposal a person’s entire bank account.
“Skimmers can be purchased on the web by sites boasting how effective their equipment is, card printing stock and equipment to make credit and debit cards is fairly easily sourced as well. All this aligns to make it pretty easy to understand why somebody with some money and no worry of arrest would want to get involved.”
Of course, as mentioned above, the original thief, the one who stole the debit/credit card information in the first place, could simply use it him or herself.
“[T]he crooks can sell the information through a contact or on the Internet, at which point counterfeit cards are made. The criminals go on a shopping spree with a cloned copy of the credit or debit card, and cardholders are unaware of the fraud until a statement arrives with purchases they did not make”
You should remember that just because card skimmers are criminals, it doesn’t mean that they aren’t business-savvy. In terms of profitability, credit card skimming can be quite lucrative since victims don’t even know their debit/credit card is compromised until it is fraudulently used. And by that time, the criminals are long gone, leaving victims with a financial mess to clean up, with no clear indication of exactly when the compromise occurred.
“Classic skimming attacks are here to stay, and will likely continue to be a problem even after banks make the shift to EMV chip cards”
– Stefan Tanase, a security researcher at Kaspersky Lab
Although EMV wasn’t designed to specifically address card skimming, the introduction of EMV in the US was optimistically predicted to decrease card skimming levels, but this has not been the case since EMV-compliant cards still hold the necessary information to conduct transactions online and at point-of-sales terminals that are not yet capable of reading chip cards.
“Thieves may still look for ways to work around the system. Also EMV cards don’t significantly improve security for online purchases, nor does the technology work when the ATM or point-of-sale terminal hasn’t been upgraded, like at many gas stations, for example.”
How to Protect Yourself from Card Skimming
Although “skimming is a world-wide problem” and skimmers “have become smller and more difficult to detect over the years”, as long as you remain vigilant anytime you make a debit/credit card transaction, you can avoid becoming a victim of card skimming.
Protect Yourself from ATM skimming
○ The most effective way to protect yourself at ATMs is to cover the keypad with your free hand as you type in your PIN so that cameras cannot capture your PIN. The majority of PINs at ATMs are captured via camera rather than a keypad overlay. Of course, this method won’t protect you from keypad overlays or from fraudulent purchases made by using your debit card as a credit card, but at least this way, criminals can’t directly access the money in your debit account.
It is even more essential that you cover the keypad as you type your PIN at non-bank ATMs, such as those found in convenience stores. It may surprise you, but there is virtually no regulation governing the purchase of a non-bank ATM – you don’t need any credentials/adhere to any regulations to buy an ATM machine! Just search for “ATM” on Ebay yourself to see just how easy it is to buy an ATM machine.
As such, you can never be sure exactly who purchased a non-bank ATM and you can never be sure who had access to the non-bank ATM.
According to the Data Breach Investigations Report released by Verizon, “in over 90 percent of the breaches in the report last year involving skimmers used a tiny hidden camera to steal the PIN”
○ Jiggle the card reader on the ATM. ATMs are built to be incredibly sturdy and solid – real ATM parts do not move even when jiggled. However, since most skimmers are attachments, jiggling them will almost always cause them to move, even if just a little.
○ Try to not use ATMs on Sundays or after Saturday morning. Weekends tend to be a favorite time for ATM skimmers since banks are not open during those times. Criminals know that banks cannot respond as quickly to suspicious ATMs when they are closed as they can when they are open. It is common for criminals to leave skimmers on ATMs over the weekend and collect their skimming equipment and data before banks open on Monday.
If the card reader on an ATM you’re about to use moves, or if you simply have a bad feeling about the ATM, do not use it.
○ Check the appearance of nearby ATMs for signs of disturbance. If the ATM you’re about to use looks different than the ATM next to it – an example of a difference would be a different-looking card reader – do not use it and report it to the bank that own the ATM as soon as possible.
○ Test the keys on the keypad to see if they are hard to push. If the keys seem oddly hard to push down, do not use the ATM since it might be compromised with a keypad overlay.
○ Check the top of the ATM near the lights, near the speakers, and the brochure holder. These are the three main places criminals tend to place the cameras used to capture PINs. PIN-capturing cameras can be so small they can capture images through a pinhole so be sure to thoroughly check those areas.

Protect yourself from credit card skimming
○ Make sure that the point-of-sale terminals do not have signs of tape or scratches. Of course, scratches could be caused by normal wear-and-tear and the presence of tape could be to address issues from normal wear-and-tear, but it’s much better to be safe than sorry.
○ Make sure that point-of-sale terminal parts do not move when you jiggle them. Most POS terminals, like ATMs, are built sturdily enough that jiggling will not cause parts to move. If any part of the terminal moves suspiciously, do not go through with the transaction.
○ At restaurants, ask to pay at the terminal as opposed to handing over your debit/credit card to your server.
○ At bars, close out your tab after each drink. Try to develop a habit of not leaving your debit/credit card with the server.
○ Do not use the furthest gas pump, especially at out-of-the-way gas stations that are seldom used. Incidences of gas pump skimming show that the furthest gas pump is a favorite target of skimmers.
Other ways to protect yourself from skimming
○ Use cash whenever possible for purchases. Yes, in today’s world cash is seen as cumbersome, but it protects you from becoming a victim to skimming.
○ Use your credit card instead of your debit card since credit cards offer you much more legal protection in the event of fraud than a debit card does
○ Turn on online/mobile fraud alerts. Most banks today have the ability to send out alerts to their customers in the event that an ATM that customers recently used may have been compromised or to send out a notification to customers that irregular charges are being conducted using their accounts.
○ Monitor all your accounts regularly for suspicious charges.
“Skimming activities can be difficult to detect. Since your credit card is never lost or stolen, the best way to detect a skimmed credit card is to watch your accounts frequently”
What to Do if Your Credit Card has been Skimmed or Stolen
If you find yourself a victim of card skimming, don’t feel too distressed - criminals are getting more and more sophisticated with their card skimming devices and techniques. Getting a debit/credit card skimmed can happen to the best of us. If you find out that one of your cards has been skimmed, here’s what you should do:
- If your debit/credit card has been stolen as opposed to skimmed, report it to the police right away. Be sure to hold onto the police report number.
- Whether your debit/credit card was skimmed or stolen, report the theft to your bank or card issuer immediately. As long as you report the fraudulent activity as soon as you notice it, you should not be held liable for the fraudulent charges.
- Monitor your accounts for additional fraudulent activity. If you notice more fraudulent activity, notify your bank/card issuer right away.
Even if your credit card hasn’t been skimmed or stolen, if you suspect that an ATM has been compromised, you should report it to the bank that owns the ATM right away.
As Timeus, a worker in a bank security department mentions: “In the future, if you ever come across a skimming device on an ATM, if you have the time, I know we appreciate a call to be notified. Trust me when I say, when a device is found, ‘alarm and whistles’ go off in my department, upper management is notified and everyone gets involved.”
Although banks and credit card issuers have protections and technology in place to address and fight card skimming activities, the first and most effective line of defense against card skimming is you, the cardholder. Skimming incidences can be stopped quickly if more people checked the ATMs and POS terminals they used for signs of tampering.
Stay vigilant out there, folks!





.png)