Recent fraud events demonstrate how a business’ reliance just on DATA to verify customer identity can enable fraud carried out by external actors along with (unfortunately) internal employees acting with malice.
Last month, scammers reached out to members of Nevada credit unions, pretending to be customer service representatives and ultimately succeeded in tricking the members to disclose personally identifying information (PII) and other financial / account information. The fraudsters deployed phishing texts and email messages from named depository institutions claiming the member’s account had been compromised, then instructing them to click on a link for more information.
The scammers used the CU’s trademarks in its phishing texts and emails to mimic the genuine online design. These ambitious and audacious criminals also reached out to their victims via phone, combining texting, phone calls and website links to make their fraud claims more believable and legitimate. Once they extracted the member’s PII the criminals exploited the information to conduct a host of financial fraud.
But perhaps even more disconcerting is the prospect (and increasing reality) of internal fraud. Companies today can stand up any number of robust security measures designed to keep criminals out of their books, but what about the malicious forces that originate from within? Navy Federal Credit Union (NFCU), the nation’s largest CU, itself fell victim in May 2022 to identity financial crimes committed by their own employees.
Two former Florida-based NFCU employees stole almost $100,000 and attempted to steal approximately $165k more after taking unauthorized screen shots of member accounts. According to investigators, a NFCU customer service representative turned-fraudster took screen shots of member account information and sent them to another NFCU employee. The co-conspirator then called the Navy Federal contact center, pretended to be the account holder, and gained access by just citing information gleaned from the screen shots.
The fraudsters then transferred funds from the compromised accounts to another NFCU member account, which was owned by a “money mule” associated with one of the co-conspirators. After the money was transferred out of the victim’s account, the funds were often times immediately transferred out of the money mule’s account into highly liquid mobile payment platforms. As many as 32 Navy Federal member accounts were compromised in this case.
Educate and Protect. Rinse and Repeat.
As an organization, there is only so much you can do to make your customers aware of fraudster activity and to prevent customers from disclosing their PII to scammers. Given the number of database breaches in the past 10+ years, it should be a default understanding by now that all of our PII data is on the DarkWeb, available to easily purchase and acquire by criminal ne’er-do-wells. To be sure, public education on fraudster tactics needs to evolve and improve, but in today’s environment businesses must assume that fraud is always reaching out, and to be wary of shaking its hand in welcome.
That said, there still (thankfully) exists a chasm from scammers having data and then using that data to conduct crimes. The criminals have to attempt to access their victim’s account information, and that’s where your business needs to have its walls fortified via fundamental best methods to authenticate identity and stop fraud in its tracks
There is simply too much at risk and too much to lose: direct funds, indirect costs, investigation costs, reputational costs. If fraud activity persists and news spreads of your weak measures, customers could lose faith in how you’re protecting their money, their identity information, etc, and defect to a competitor.
Speed Kills
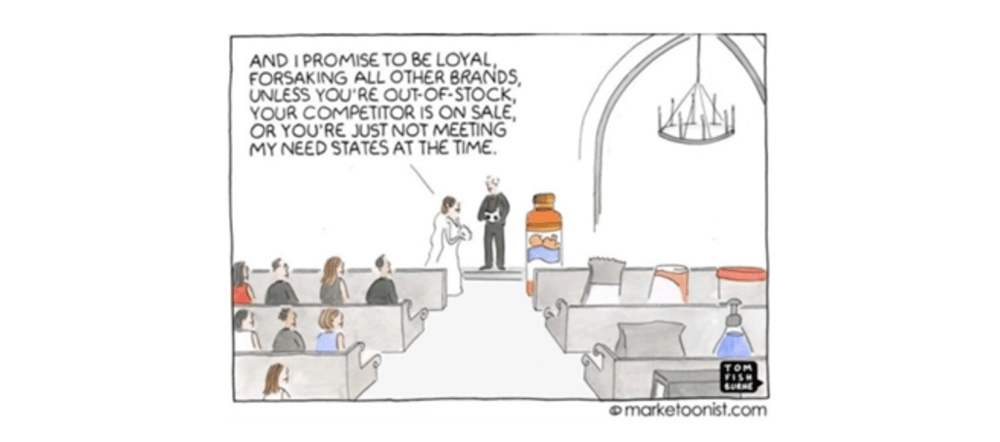
In the cadence of a busy day, fraudsters count on companies being focused on the business at hand, building for the future vs. protecting the now, and easing transactional friction for their customers. To stay competitive, organizations prioritize speed and convenience and immediate gratification to serve a non-loyal customer base.
There are real consequences when employees are pressed and stressed for productivity and efficiency metrics. As we recall from the infamous Y2011 Wells Fargo account fraud scandal, a myopic focus on process and transaction speed promotes errors, and can also enable outright (in this case, internal) fraud. In the pursuit of speed, Wells Fargo management pressured their bankers to open as many accounts as possible to produce sales against extremely aggressive and even mathematically impossible quotas, and turned a blind eye to how it was getting done.
Its bankers created millions of fraudulent savings and checking accounts on behalf of Wells Fargo clients without their consent. In 2016 the Consumer Financial Protection Bureau (CFPB) fined Wells Fargo $185 million as a result of the illegal activity. By the end of 2018, the company faced additional civil and criminal suits reaching an estimated $2.7 billion. And as of late last year, 2021, the creation of these fake accounts continued to have legal and financial ramifications for Wells Fargo and former bank executives.
In our previous “Cell Phone Double Whammy” article, we wrote about fraudster Henry Perez who gained access to and control of cellular service provider accounts just by verifying personal data information, and then turned around and charged hundreds of thousands of dollars worth of iPhones to the genuine account owners. These expensive devices would then be ordered and shipped to him or his co-conspirators, or in some cases Henry would stride right into a physical store and pick them up.
How did Henry Perez manage this? Again, tremendous sales and transaction pressure, combined with assumptions that “provided data is enough” enabled a process and culture that de-prioritized security and created gaps big enough to drive a metaphorical truck through.
At UVeritech, we continue to see how too many companies operate under the erroneous assumption that “technology alone can save the day”, by just using “data” to validate a person’s identity. This is a fundamentally flawed methodology since this abstract, un-linked, un-personalized data is not automatically connected to YOUR customer, just to SOME identity. This identity could be a fraudster just as much as it could be your genuine customer. This identity might not even be real, just a manufactured, synthetic identity.
In the pursuit of speed, of efficient processes, a leapfrog over fundamental identity document authentication processes can and does lead to fraud. This loss is entirely preventable by augmenting your existing policies and procedures with a forensic level identity document authentication process.
Contact us. Let us help you know your customer, reduce risks, and protect your reputation.



